DevSecOps: Meaning, How It Works, Benefits and DevOps
DevSecOps embeds security into the software delivery lifecycle. This article covers what DevSecOps is, how it differs from DevOps, how it fits into CI/CD, core principles, best practices, common tools, and how cloud native and AI trends are shaping modern DevSecOps.
What is DevSecOps?
DevSecOps stands for development, security, and operations. It is a software development approach where development and operations teams and the security team integrate security into the DevOps pipeline so that security checks, security scanning, and automated security testing (for example, static application security testing and dynamic application security testing) run at every stage of the software development lifecycle. This “shift left” model makes developers and operations jointly responsible for addressing security vulnerabilities, producing secure code, and meeting compliance while keeping delivery fast.
DevSecOps vs DevOps: What’s the Key Differences?
DevOps optimises delivery speed and reliability, while DevSecOps adds integrated, continuous security as a shared responsibility across the development team, operations, and the devsecops team.
How does the DevSecOps lifecycle work?
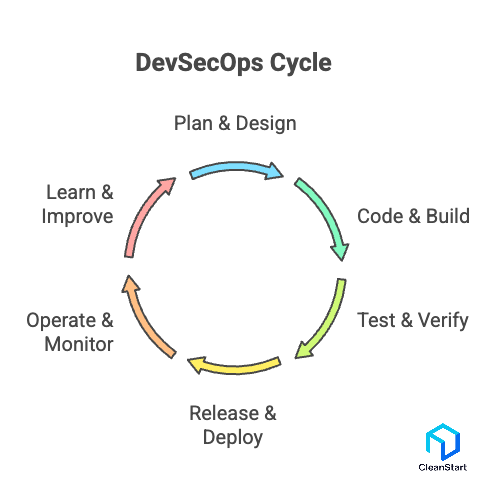
DevSecOps runs as a continuous loop that integrates security practices into every phase of the software development life cycle, so DevOps teams treat security as part of delivery, not an afterthought. The DevSecOps framework typically follows six connected stages that feed into each other.
Here are the main stages and how they work together:
- Plan & design – Teams define security policies, security controls, and risks up front, so you implement DevSecOps as requirements, not patches.
- Code & build – Developers apply secure development practices while DevSecOps tools scan code and dependencies for software security issues during builds.
- Test & verify – Automated checks (including security automation and interactive security tests) validate behaviour and address security issues before release.
- Release & deploy – Pipelines enforce policy gates; only builds that meet security and compliance criteria move to production, embedding security into the software delivery pipeline.
- Operate & monitor – Runtime monitoring, logging, and alerts track security posture in the live DevSecOps environment, feeding real incidents back to teams.
- Learn & improve – Post-incident reviews and DevSecOps culture practices refine rules, tooling, and training, improving the next cycle throughout the software development process.
What core benefits does DevSecOps bring?
DevSecOps brings clear, practical advantages to modern software teams by making security practices part of everyday delivery work, not a separate afterthought. By shifting security into the pipeline and using automation and integrated security tools, teams ship faster while reducing real-world risk.
Here are the core benefits DevSecOps provides:
- Earlier detection of security issues
Security checks run during coding, build, and test, so security issues are caught when they are cheaper and easier to fix.
- Consistent, enforceable security practices
Teams implement security practices as standard steps in the workflow, ensuring the same controls run on every change instead of relying on ad-hoc reviews.
- Security at scale through automation
Pipeline automation continuously triggers scans, policies, and validations, keeping coverage high without slowing the team down.
- Better leverage of security tools
When security tools are integrated into CI/CD, they deliver continuous visibility rather than one-off reports, reducing blind spots across services and environments.
- Improved reliability and confidence in releases
Because security checks are built into the process, releases are less likely to introduce critical vulnerabilities, giving teams and stakeholders greater confidence in each deployment.
How security is embedded into CI/CD?
Security is embedded into CI/CD by using a DevSecOps approach as an approach that integrates security practices directly into each phase of the DevOps pipeline, so every code change is automatically checked for risk as part of normal delivery, not after application development is done.
Here’s how it works in a concise, practical way:
- CI/CD pipelines devsecops integrate security best practices as named jobs (linting, dependency checks, interactive application security tests) that scan software for security issues on every commit, enabling secure software development.
- Policy and quality gates enforce compliance with security by failing builds when vulnerabilities or misconfigurations are detected, turning the pipeline into one of the core components of DevSecOps.
- Shared dashboards and automated feedback align DevOps and security, strengthening collaboration between development and security teams and making DevSecOps adoption stick, which is where the real benefits of DevSecOps come from.
What Does a Modern DevSecOps Architecture Look Like?
A modern DevSecOps architecture is a unified DevOps security stack where the devsecops model is defined around one core idea: the integration of security practices into code, CI/CD, infrastructure, and operations, so you maintain security throughout the development lifecycle instead of bolting it on at the end.
Here are the key elements of a modern DevSecOps architecture:
- Integrated CI/CD and security pipeline
The CI/CD system is wired with scanners, policy checks, and approvals, so DevSecOps introduces security gates directly into build, test, and deployment stages.
- Centralised security services layer
Identity, secrets management, vulnerability management, and policy engines are shared services called from pipelines and platforms, enforcing DevSecOps best practices consistently.
- Unified observability and runtime protection
Logs, metrics, traces, and threat detection tools feed into the same platform, so production incidents continuously inform the implementation of DevSecOps.
- Standardised guardrails and configurations
Reusable templates for infrastructure, containers, and app configs make the best DevSecOps setups repeatable, reducing drift and misconfiguration risk.
- Collaboration and workflow integration
Tickets, alerts, and findings are linked to backlogs so that adopt DevSecOps means development, operations, and security teams work from the same data and workflows.
- People and culture layer
Structured security training and clear roles make DevSecOps important culturally as well as technically, so the architecture supports behaviour change, not just tools.
What Core Principles Define an Effective DevSecOps Approach?
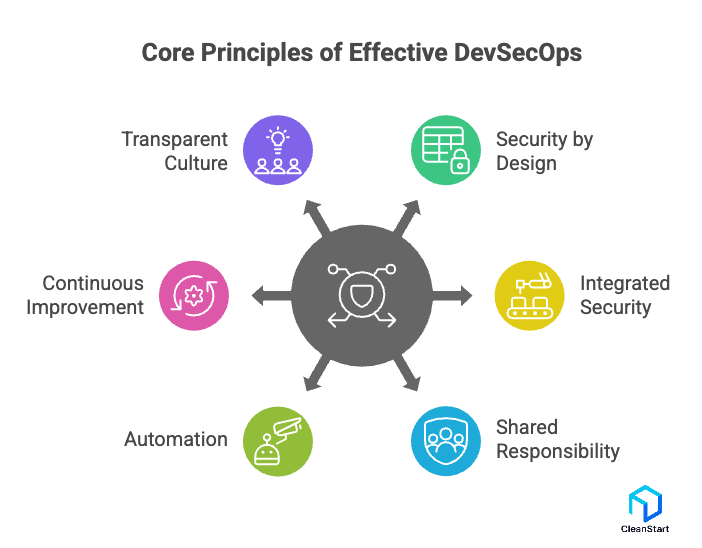
An effective DevSecOps approach is defined by a small set of non-negotiable principles that turn security into a built-in property of how teams design, build, and run software, not an external audit step. When these principles are in place, DevSecOps makes security measurable, repeatable, and aligned with delivery speed instead of fighting it.
Here are the core principles that define an effective DevSecOps approach:
- Security by design, not by afterthought
Security requirements, abuse cases, and controls are captured at the design stage, so features are shaped around secure assumptions from day one.
- Security integrated into every pipeline, every change
All code, configs, and dependencies pass through the same automated checks; no change bypasses security just to “move fast”.
- Shared responsibility across development, operations, and security
Security outcomes are owned jointly, with clear roles and metrics, rather than pushed onto a separate team at the end.
- Automation over manual enforcement
Policy, scanning, and validation are codified and automated so they run consistently on every commit and build, removing reliance on ad-hoc reviews.
- Continuous feedback and improvement
Findings from tests, incidents, and audits feed back into design, tooling, and playbooks, creating a closed loop that tightens controls over time.
- Culture of transparency and learning, not blame
Issues and near-misses are surfaced openly, used to improve guardrails and habits, and not hidden to “protect” teams or release dates.
What Are the Key DevSecOps Principles and Best Practices Teams Should Follow?
When DevSecOps is defined properly, a few core principles and best practices keep security built into everyday work instead of treating it as a gate at the end.
Key DevSecOps principles and best practices:
- Security by design – Define security requirements and threats at design time so features start from secure assumptions.
- Shift security left – Move reviews, threat modelling, and automated checks into planning, coding, and build stages.
- Automation first – Automate security scans, policy checks, and approvals in CI/CD so every change is evaluated consistently.
- Shared responsibility – Make security a joint outcome for development, operations, and security with clear ownership.
- Policy as code – Express security rules as code so they are versioned, testable, and reusable across environments.
- Continuous monitoring and learning – Use logs, alerts, and incidents to refine controls and improve DevSecOps over time.
What Tools and Automation Strategies Power an Effective DevSecOps Workflow?
When DevSecOps is defined as security built into the delivery pipeline, an effective workflow depends on two things working together: the right tool categories and opinionated automation strategies that run on every change with minimal manual effort.
Core tool categories in an effective DevSecOps workflow
- Code and dependency scanners – SAST and software composition analysis to catch insecure code and vulnerable libraries early.
- App and API security testing – DAST and interactive testing to probe running applications and APIs for real-world weaknesses.
- Infrastructure and config security – IaC scanners and cloud posture tools to prevent misconfigurations before and after deployment.
- Secrets and identity management – Secrets managers and IAM integrations to keep credentials out of code and enforce least privilege.
- Monitoring and analytics – Central logging and security analytics to detect incidents and feed improvements back into the pipeline.
Key automation strategies that make these tools effective
- Security-as-pipeline-steps – Standard security jobs wired into CI/CD so every commit runs the same checks.
- Policy-as-code gates – Security rules expressed as code and enforced automatically to pass or fail builds.
- Risk-based gating – Clear thresholds (for example, block on critical issues) so releases are decided by objective signals.
- Inline feedback to developers – Scan results surfaced in pull requests and issues so fixes happen in context.
- Closed-loop learning – Production alerts automatically inform new rules, tests, or controls, tightening DevSecOps over time.
How Does DevSecOps Enable Secure and Scalable Cloud-Native Environments?
DevSecOps enables secure, scalable cloud-native environments by making security a built-in property of how teams design, deploy, and operate containers, Kubernetes workloads, and managed cloud services. Containers package applications with their dependencies into portable, isolated units, and DevSecOps ensures security is embedded into container build pipelines, image management, orchestration, and runtime operations. With DevSecOps defined as security integrated across pipelines, platforms, and container runtime controls, cloud-native systems can scale rapidly without losing visibility or control over risk.
Container images act as the immutable delivery unit in cloud-native DevSecOps workflows, flowing from build to registry to runtime, with security controls such as image scanning, signing, and policy enforcement applied once and trusted everywhere the image is deployed.
Here is how DevSecOps does this in practice:
- Infrastructure and security as code
Cloud resources, network policies, and controls are declared as code, so every cluster, namespace, or service follows the same secure baseline and can be recreated or scaled safely.
- Security embedded in CI/CD for containers and microservices
Images, Helm charts, and IaC templates are scanned in the pipeline, ensuring that vulnerable images, overly permissive configs, or misconfigured secrets never reach production.
- Automated, policy-driven guardrails instead of manual checks
Admission controllers, policy engines, and runtime controls enforce rules (for example, allowed registries, required encryption, non-root containers) automatically across clusters and regions.
- Continuous runtime monitoring and feedback loops
Telemetry from container runtimes, service meshes, and cloud logs feeds into security analytics, so suspicious behaviour in one environment quickly informs new rules and tests for all.
- Shared ownership between platform, security, and product teams
Platform teams provide secure defaults, security teams define policies and detection logic, and product teams ship changes through guarded pipelines, keeping both scalability and security aligned.
What Trends and Advancements Will Shape the Future of DevSecOps?
The future of DevSecOps is moving toward more intelligent automation, deeper supply chain protection, and developer-friendly security built into everyday work, not layered on top.
Here are the main trends and advancements that will shape DevSecOps:
- AI-driven security operations – AI and ML will prioritise vulnerabilities, reduce alert noise, suggest fixes, and even open remediation pull requests, turning raw findings into guided actions.
- Supply chain security and SBOM by default – SBOMs, artefact signing, and provenance checks will become standard gates so only verified images and packages reach production.
- Policy-as-code and compliance-as-code – Security and compliance rules will be written as code, enforced automatically in CI/CD, and used to generate audit evidence directly from pipeline logs.
- Developer-first security UX – Security feedback will surface in IDEs and pull requests, backed by secure templates and guardrails that make the secure path the easiest path.
- Cloud-native and runtime-aware controls – DevSecOps will lean on Kubernetes policies, which define and enforce security rules at the cluster and workload level, service meshes, and runtime telemetry to enforce security based on real workload behaviour, not just static configs.
- End-to-end automation with human override – Pipelines will make risk-based release decisions automatically; humans will tune policies and handle exceptions instead of manually approving every change.
- Unified security data fabric – Code scans, pipeline events, and runtime alerts will feed into a single correlated view, linking vulnerable code to deployed services and real incidents.
- Stronger shared ownership models – Embedded security engineers, security champions, and shared KPIs will make DevSecOps a permanent operating model, not a one-off initiative.
How Are AI and Automation Transforming the DevSecOps Workflow?
AI and automation are transforming the DevSecOps workflow by turning security into a continuous, data driven system that runs at the same speed as modern delivery instead of acting as a slow manual checkpoint.
Here is how they change the workflow in practice:
- Smarter triage instead of alert overload
AI engines correlate scanner results, logs and cloud events to remove duplicates and highlight the vulnerabilities that actually matter for each service.
- Faster fixes with suggested remediation
For common issues such as insecure configurations, dependency upgrades and policy gaps, AI can propose code patches or configuration changes so engineers review and apply rather than start from scratch.
- Automated policy enforcement in CI CD
Pipelines use policy as code gates for example block critical issues that run on every commit, and automation enforces these rules consistently without manual approvals.
- Proactive detection and response at runtime
AI driven analytics watch live behaviour for anomalies and can trigger automated actions such as raising incidents, blocking traffic or rolling back releases so response time shrinks from days to minutes.
FAQ’S
1.Does DevSecOps require coding?
Yes. DevSecOps typically requires some coding (mostly scripting and configuration-as-code) to automate security checks in CI/CD, manage IaC, and maintain policies, but not everyone on the team must code.
2.How do you measure DevSecOps success?
Measure DevSecOps with a small set of security and delivery KPIs together: vulnerability time to remediate (MTTR), escape rate (vulns found after release), build pass rate with security gates, policy exception volume, incident frequency, and time to detect and respond (MTTD, MTTR).
3. What are the biggest challenges in DevSecOps adoption?
Common blockers are tool noise and false positives, unclear ownership between teams, slow pipelines due to heavy scans, weak secrets hygiene, inconsistent IaC standards, and lack of risk-based gating that prioritizes what truly blocks releases.
4. What is “policy as code” in DevSecOps?
Policy as code means writing security and compliance rules in version-controlled, testable code so they can be enforced automatically in CI/CD and at runtime, with consistent outcomes across environments and repeatable audit evidence.
5.How do you handle false positives and alert fatigue in DevSecOps?
Use risk-based triage and tuning: define severity thresholds for gating, suppress known-benign findings with documented justification, create allowlists with expiry, prioritize exploitable issues, and continuously tune rules based on production signals and developer feedback.



