Most teams have shift-left security figured out on paper. Code scanning in the IDE, dependency checks on commit, image scanning before push, policy gates before deploy. The pipeline looks mature.
But there's a question most of those pipelines never ask: what's in the base image everything is being built on top of?
If your CI/CD process starts with a bloated, uninspected, or inherited image, every downstream control is working harder than it should. You're not shifting security left. You're adding more detection steps on top of a shaky foundation
That is why hardened container images matter. And that is where CleanStart fits.
CleanStart is not another scanner added later in the pipeline. It helps organizations begin with cleaner, verifiable, lower-risk images so security starts at the source, not after problems are introduced.
The Hidden Gap in Many CI/CD Pipelines
A common modern pipeline looks like this:

Those orange nodes (scanning and runtime monitoring) are doing important work. But notice what they're working on: an image that already exists. The image was assembled from a base that came from somewhere upstream. That base is carrying whatever it was built with.
In practice, that means your image probably contains:
- Unnecessary packages and utilities
- Inherited components no one actively manages
- Shell access that increases post-compromise risk
- Writable filesystems that enable tampering
- Excess complexity that expands the attack surface
Security tools later in the pipeline may detect issues. But they usually do not remove the architectural risk already baked into the image.
That means many teams are shifting left on scanning, while still starting dirty.
Shift Left: Detection vs Prevention
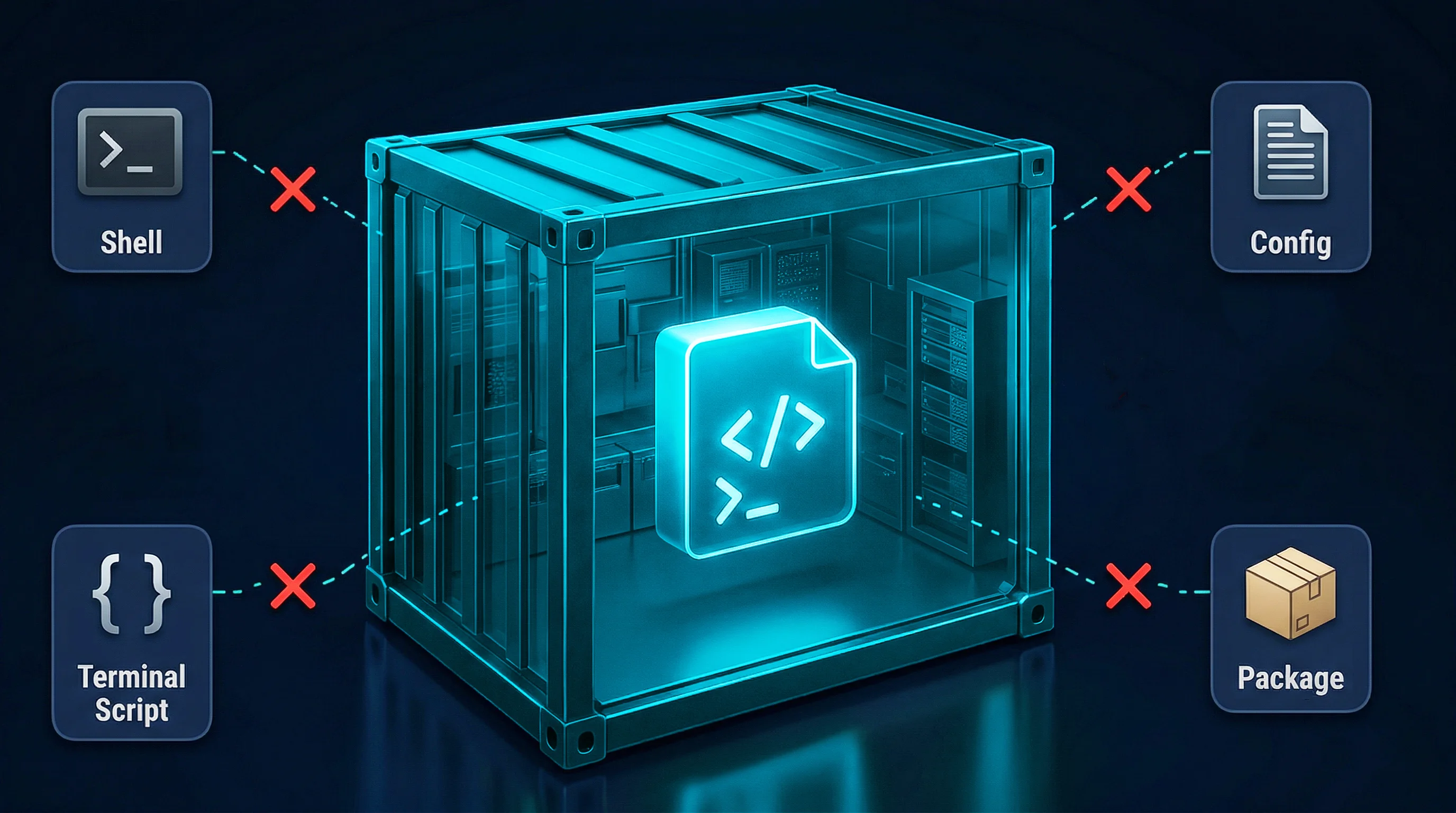
Many organizations define shift left as:

These controls improve earlier detection.
But a stronger model focuses on prevention:

The difference matters.
When the base starts clean — source-built, without inherited CVEs, with a cryptographic provenance trail — every downstream stage has less to compensate for. Scanners still run, but they're verifying a clean image instead of triaging a noisy one. Now we see how this model works with CleanStart
CleanStart belongs at the image creation stage, before artifacts are promoted downstream.
The stronger pipeline model is:
Code → Build on CleanStart Trusted Base → Validate → Sign → Registry → Deploy → Runtime
This changes the role of security.
Instead of asking, “How do we secure this image later?” the question becomes:
Why introduce avoidable risk into the pipeline at all?
For developers, this often means replacing base image standards rather than redesigning existing CI/CD tooling.
For security leaders, it means fewer downstream exceptions, less remediation overhead, and stronger supply chain confidence.
What Developers Gain by Starting Clean
Engineering teams care about speed, stability, and simplicity. Hardened images need to support those goals.
CleanStart is designed to integrate into existing workflows rather than force process disruption.
That means teams can adopt stronger images without redesigning pipelines or slowing delivery.
Benefits for developers include:
Smaller, Purpose-Built Images
By replacing standard utility-heavy userland layers with CleanStart_Util, only required components are included. This reduces unnecessary footprint and operational noise.
More Predictable Runtime Behavior
Fewer inherited components means fewer surprises across environments.
Less Security Rework Later
When cleaner images enter the registry, teams spend less time triaging avoidable issues downstream.
No Need to Bolt Security On Later
Security becomes part of the artifact, not another ticket after the build completes.
What CXOs Risk by Getting This Wrong
Executives often ask a different question: What happens if we do nothing?
The answer is operational drag and avoidable risk.
Rising Remediation Costs
If insecure or overly complex images flow through the pipeline, every later stage becomes more expensive:
- More findings to review
- More policy exceptions
- More deployment friction
- More runtime alerts
- More engineering time spent on rework
Late-stage image issues often surface near release windows, where remediation is most expensive. Security findings discovered after QA, staging, or approval cycles can delay launches, consume engineering hours, and create avoidable friction between security and delivery teams.
Slower Delivery Velocity
Security added late creates friction near release deadlines, where delays are most expensive.
Increased Breach Exposure
If a compromised container includes shell access or writable filesystems, attackers gain more options for movement, persistence, or tampering.
Weak Supply Chain Confidence
Boards and leadership increasingly ask how software is built, not just whether it was scanned.
If the answer begins with inherited public images and reactive controls, confidence is limited.
Why Shift Left Is Incomplete Without Starting Clean
Many organizations define shift left as:
- Earlier scanning
- Earlier testing
- Earlier policy checks
Those matter.
But if the image itself begins with avoidable risk, then security is still reacting to upstream decisions.
True shift left means reducing risk before the image is created, not only detecting issues after creation.
That is the strategic role of CleanStart.
It enables teams to start with hardened, verifiable images that move through CI/CD with stronger security properties already in place.
How CleanStart Changes the Starting Point
Most security controls in CI/CD are designed to validate or restrict what already exists.
CleanStart shifts that model by improving what enters the pipeline in the first place.
Instead of inheriting general-purpose container images and trying to secure them later, teams can begin with images designed for production runtime from the start.
This changes how downstream controls behave:
- scanners focus on relevant issues instead of inherited noise
- policies enforce intent rather than compensate for weak defaults
- runtime controls operate on smaller, more predictable surfaces
The result is not just earlier detection, but less risk introduced into the pipeline to begin with.
The Conversation That Matters
When evaluating hardened images, many teams ask: Do we really need this if we already scan containers?
A better question is: Why continue building on risky foundations and paying to fix it later?
Scanning, policies, and runtime monitoring remain important.
But none of them replace starting with a cleaner image.
Final Thought
Every container deployed to production starts as an image moving through CI/CD.
That makes the image the earliest scalable control point in your software delivery process.
If your shift-left strategy begins after the image is already built, you are detecting inherited risk, not preventing it.
See how hardened images fit into CI/CD pipelines
Start clean. Build secure. Reduce risk before it spreads.

.svg)
.webp)
.png)



.webp)
.webp)