Image Repository: Definition, Works, Configuration, Selection and Risks
Container images need a safe, consistent place to live and move. This article covers what an image repository is, how registries store and secure images, how to choose a repository, write an ImageRepository spec, read status fields, and manage it in operations. It also outlines key security risks and the registry vs repository difference.
What Is an Image Repository?
An image repository is a structured storage location that holds versioned container images and makes them available for retrieval through a registry interface. It contains complete containers, which are lightweight, isolated user-space environments that package an application with its dependencies and a minimal filesystem. Containers run directly on the host operating system using namespaces for isolation and cgroups for resource limits, providing a portable, consistent, and efficient runtime. By storing container images in an image repository, developers and systems can reliably push, pull, and deploy containers across environments while ensuring every deployment uses a verified and immutable image.
How Does Image Repository Work?
- An image repository stores versioned Docker images in a namespace and exposes them through a registry service for reliable push and pull operations.
- When an image is pushed, the repository stores layers using OCI standards and assigns tags.
- Access uses authentication methods such as AWS IAM, Azure identities, or Kubernetes service accounts to enforce access control.
- Repositories exist in public registries like Docker Hub, Amazon ECR, ACR, and GCR, or as private provider-managed systems.
- Users interact via CLI commands to download, reuse, and manage stored artifacts.
- Public repositories let developers browse catalogs, while enterprise platforms add TLS, geo-replication, and compliance features.
- Many registries include image vulnerability scanning for base images and application layers.
- Kubernetes pulls images during deploy operations, completing the repository lifecycle.
Which Container Image Repository Should You Choose?
Choosing the right container image repository depends on how well the platform aligns with your security requirements, deployment workflows, and ecosystem integration within a containerization strategy. A suitable repository should provide predictable performance, enforce strong access control, and support automation at scale as containerized applications move through build, test, and production stages. The best choice is the one that fits your operational environment, whether you’re running Kubernetes clusters, leveraging cloud-native services, or managing mixed workloads across multiple providers, all of which rely on consistent containerization to package applications and their dependencies in a portable, repeatable way.
Key considerations include:
- Whether the registry integrates cleanly with your cloud platform or CI/CD pipelines.
- How it enforces authentication, permission boundaries, and protection of sensitive images, especially in environments where workload isolation relies on primitives like cgroups, which limit and account for CPU, memory, and I/O resources to keep containerized workloads isolated and prevent one container from impacting another.
- The maturity of its vulnerability scanning, remediation features, and compliance safeguards.
- Support for geo-replication, caching, and high availability across regions.
- Its pricing model and suitability for long-term growth as your image catalog expands.
How Do You Write an Image Repository Specification?
You write an ImageRepository specification by defining the fields that control how the repository is discovered, authenticated, and scanned within your automation or GitOps workflow. The spec outlines the image source, the scan interval, the access method, and the security parameters required to manage images consistently. It provides a declarative structure that ensures every reconciliation event uses the same configuration, supporting predictable behavior when the container entrypoint, which defines the default command and runtime behavior executed when a container starts, is executed during deployment.
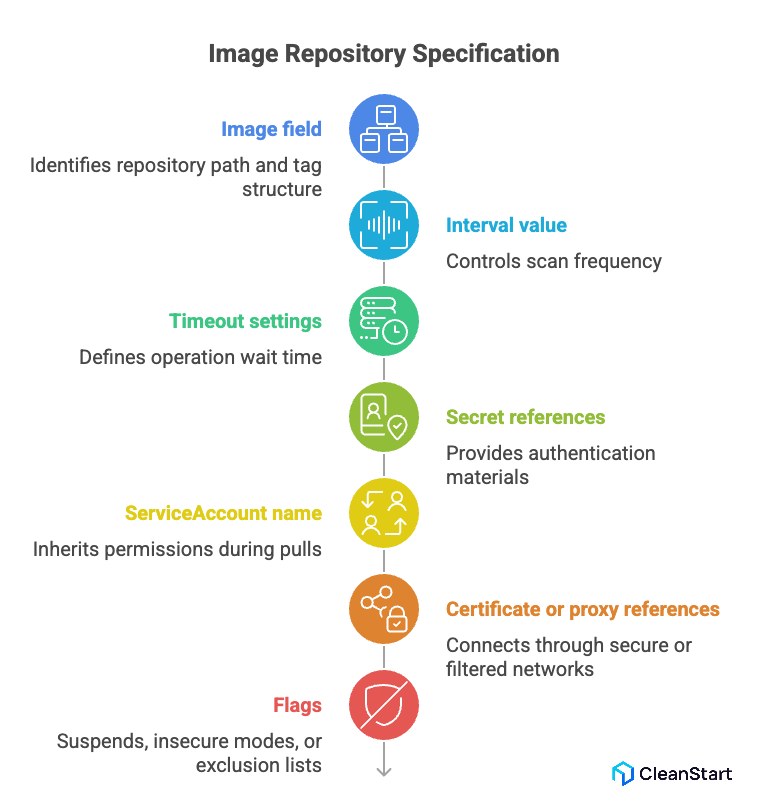
Key elements to include are:
- The image field that identifies the repository path and tag structure.
- The interval value that controls how frequently scans occur.
- Timeout settings that define how long the controller waits before failing an operation.
- Secret references for authentication materials such as tokens or credentials.
- The ServiceAccount name used to inherit permissions during pulls.
- Certificate or proxy references when connecting through secure or filtered networks.
- Flags for suspend, insecure modes, or exclusion lists depending on policy requirements.
What Security Risks Exist in Container Image Repositories?
Security risks in container image repositories arise when unverified images, weak access controls, or outdated components enter the deployment pipeline. A repository becomes a high-impact attack surface because it distributes the artifacts that every workload depends on, especially in environments driven by container orchestration, where platforms automatically schedule, scale, and manage containers across clusters. If the images inside it are compromised, every environment that pulls from the repository inherits that risk.
Common risks include:
- Unscanned or outdated images that contain known vulnerabilities or unpatched base layers.
- Weak authentication that allows unauthorized access or accidental exposure of private images.
- Misconfigured permissions that enable broad write access or allow tampering with tags.
- Supply chain compromises, where attackers inject malicious content into trusted images.
- Public image misuse, where teams pull unverified open-source images without validating integrity.
- Lack of remediation workflows, causing vulnerable images to remain in circulation.
Image Registry vs. Repository: What is the difference?
How Do You Work with Image Repositories Operationally?
You work with ImageRepositories operationally by managing how they reconcile, authenticate, and surface status information throughout their lifecycle. The goal is to keep image metadata current, ensure access is reliable, and maintain predictable behavior during deployments, especially as each container runtime, which is responsible for pulling images, creating containers, and executing them in isolation on the host system, pulls and executes images in production environments.
Key operational actions include:
- Triggering a reconcile event when you need the system to refresh tags or rescan the source.
- Checking readiness conditions to confirm that authentication, connectivity, and scanning have succeeded.
- Suspending an ImageRepository when you want to pause updates without removing the resource.
- Resuming the repository when scans and reconciliations should start again.
- Using describe and event logs to debug failures related to credentials, upstream errors, or network issues.
How Do You Interpret ImageRepository Status Fields?
You interpret ImageRepository status fields by reviewing the signals that indicate scan behavior, authentication outcomes, and overall resource health. Each field reflects a specific point in the controller’s decision-making process and helps you diagnose whether the repository is functioning as expected, especially when correlating scan results with SBOM data, which provides a detailed inventory of software components and dependencies inside an image to validate the integrity of image components.
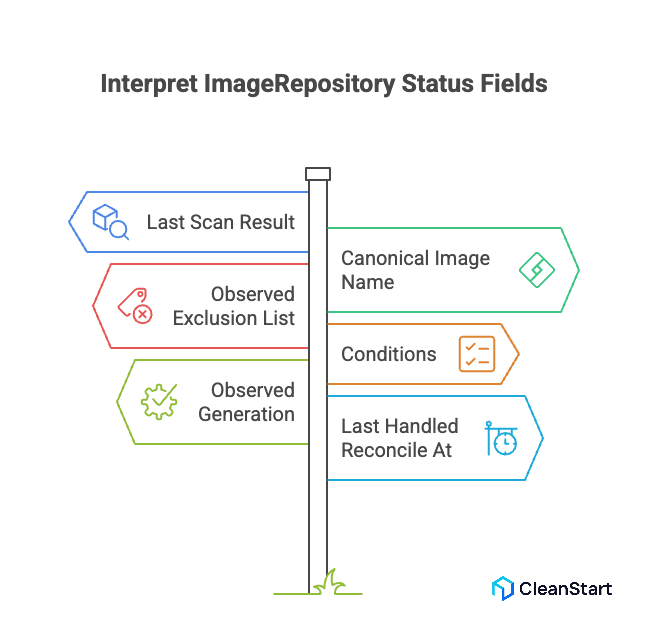
Key fields to evaluate include:
- Last Scan Result, which shows whether the most recent image discovery or tag fetch succeeded.
- Canonical Image Name, confirming the normalized reference the system uses internally.
- Observed Exclusion List, indicating which tags or patterns were filtered out based on policy.
- Conditions, which outline states such as reconciling, ready, or failed with precise reasons.
- Observed Generation, showing whether the controller has processed the latest spec update.
- Last Handled Reconcile At, helping you check when the resource was last evaluated.
FAQs
1. How is an image tag different from an image digest?
An image tag is a human-readable version label, while a digest is the immutable cryptographic identifier of the exact image content.
2. Can multiple services pull from the same image repository simultaneously?
Yes. Image repositories support concurrent pull operations, and registry backends handle parallel requests without affecting the image’s integrity.
3. What happens if an image push is interrupted during upload?
The registry stores partial layers temporarily but will not publish the image until all layers and the manifest are fully uploaded and validated.
4. Do private repositories support geo-replication?
Most enterprise registries support geo-replication to keep images close to deployment regions, improving availability and reducing pull latency.
5. How long should image versions be retained in a repository?
Retention depends on your deployment lifecycle. Many teams keep active versions and prune unused tags using automated clean-up policies or lifecycle rules.



