NIST SP 800 171 Compliance for CUI in Containerized Systems
Handling CUI in containerized systems can get complicated fast. This guide breaks down what NIST SP 800-171 is, who must comply, the compliance checklist, control families, Rev 3 vs Rev 2 changes, 800-171 vs 800-53, DoD assessment and 800-171A, and how to protect CUI on media.
What is NIST SP 800-171 compliance for CUI?
NIST SP 800-171 compliance for CUI means implementing the security requirements in the NIST Special Publication (SP) 800-171 to protecting controlled unclassified information when that information resides in nonfederal systems and organizations (that is, unclassified information in nonfederal systems owned or operated by contractors, suppliers, universities, and other private or nonfederal systems and organizations). The standard’s core purpose is protecting the confidentiality of controlled unclassified information in nonfederal environments by requiring a defined set of security controls (requirements) for the relevant parts of the information systems that process, store, or transmit CUI, or that provide protection for those components.
Compliance with NIST SP 800-171 typically means you can demonstrate, with documented evidence suitable for audit, that your nonfederal information system meets the applicable 800-171 requirements, including how each container workload that processes or stores CUI is configured, isolated, logged, and controlled to protect confidentiality, and that these requirements are flowed down by federal agencies through contracts and agreements. For DoD contractors, this is commonly tied to DFARS clauses that reference NIST SP 800-171 requirements, including incident reporting and assessment-related obligations.
What is the NIST standard for CUI?
The NIST standard for CUI is NIST Special Publication 800-171, which defines the security requirements organizations must implement to safeguard Controlled Unclassified Information when it is stored, processed, or transmitted outside federal networks, including verifying that the container entrypoint that starts the application process is locked down to run only approved commands and prevents unauthorized shell access paths that could expose CUI. It applies primarily to contractors and partners handling federal information in nonfederal environments.
What is the NIST 800-171 compliance checklist?
The NIST 800-171 compliance checklist is a structured, evidence-based set of steps an organization uses to comply with NIST SP 800-171 by implementing and verifying the NIST 800-171 requirements for protecting the confidentiality of CUI when the information is resident in nonfederal systems and operated by nonfederal organizations, including validating that each container image used to package and deploy applications handling CUI is hardened, access-controlled, scanned, and monitored to prevent unauthorized exposure. NIST describes these as recommended security requirements for protecting the confidentiality of CUI in nonfederal systems and organizations.
The following points are related to compliance with NIST 800-171 for CUI in nonfederal environments.
Define scope for CUI in your environment
- Identify where CUI when the information is resident in your environment (apps, endpoints, servers, cloud accounts, storage, backups, logs).
- Determine which components of nonfederal systems process, store, transmit, or provide protection for such components that handle CUI.
Confirm the governing baseline and revision
- Select the applicable SP 800-171 rev baseline you are targeting (commonly 800-171 revision 2 for many DoD programs; revision 3 is published by NIST and may require transition planning depending on contract language).
Implement the NIST SP 800-171 security requirements (control families)
- Implement required safeguards across the SP 800-171 families for information systems and organizations that handle CUI, including access control, identification/authentication, audit, configuration management, incident response, media protection, and other requirements for protecting the confidentiality.
Enforce least privilege for CUI access
- Apply the principle of least privilege so only authorized roles have access to the system and can access CUI needed for their job function.
Configure auditability and retention
- Enable audit logging for CUI-relevant events (authentication, privilege changes, access attempts, admin actions) and retain logs to support investigations and to demonstrate compliance during assessments.
Protect media that contains CUI
- Inventory, physically control and securely store media containing CUI, restrict transport, and define sanitization and disposal so teams do not inadvertently share sensitive information through removable media or retired assets.
Create and maintain documented security plans
- Maintain a System Security Plan and supporting security plans that describe implemented controls, system boundaries, roles, and how CUI is protected end-to-end.
Assess using NIST Special Publication 800-171A
- Use NIST Special Publication 800-171A assessment procedures to collect objective evidence and validate whether each requirement is satisfied.
Track gaps and corrective actions
- Document unmet controls, remediation tasks, and timelines so you can show a managed path to achieving and maintaining NIST compliance rather than one-time implementation.
Align with DoD and acquisition requirements when applicable
- If you are a DoD contractor, ensure your checklist aligns with contract obligations under the Defense Federal Acquisition Regulation Supplement, and map requirements to CMMC Level 2 expectations when required for contract eligibility.
Validate data types within scope
- Confirm how CUI categories overlap with other regulated data (for example personally identifiable information) and ensure controls cover both the CUI handling workflow and any additional policy constraints for the CUI category.
Use NIST 800-53 mappings as supporting reference, not a substitute
- Where useful, reference mappings to NIST 800-53 controls to strengthen traceability, but treat SP 800-171 as the authoritative requirement set for CUI in nonfederal environments unless a contract explicitly requires compliance with NIST 800-53.
What is NIST SP 800-171?
NIST SP 800-171 is a cybersecurity standard from the National Institute of Standards and Technology (the U.S. Institute of Standards and Technology) that specifies information security requirements for protecting the confidentiality of CUI when controlled unclassified information is resident in nonfederal systems and organizations. It is written so federal agencies can flow these compliance requirements into contracts and agreements with organizations that process CUI outside federal networks.
800-171 provides a consistent set of recommended security requirements that help ensure CUI stored on digital systems (and the supporting systems that protect it) remains protected in nonfederal environments, including container security controls that harden containerized workloads, restrict CUI access paths, and reduce exposure from misconfigurations or vulnerable components. This is of paramount importance to federal agencies because CUI often supports essential missions and functions. The scope is tied to the policy for the CUI category listed in the CUI Registry, and it applies when the nonfederal organization is not collecting or maintaining information or maintaining information on behalf of a federal agency or operating a system on behalf of an agency.
How do you protect CUI on digital and non-digital media under NIST 800-171?
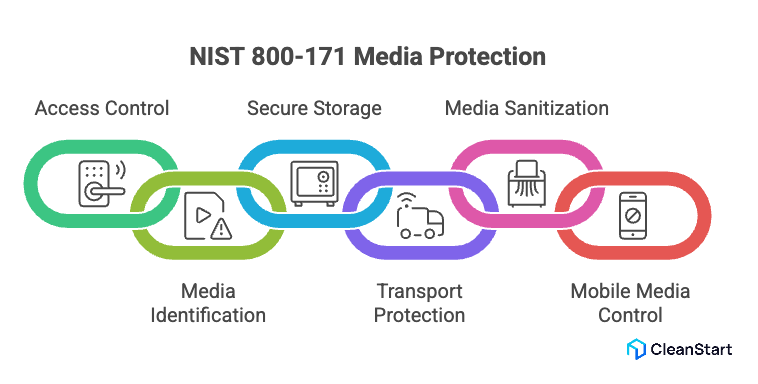
Protecting CUI on digital and non-digital media under NIST 800-171 means implementing media protection controls that prevent unauthorized access, exposure, transfer, or loss of sensitive data across physical and electronic environments. The objective is to ensure CUI remains protected wherever it exists—devices, storage media, printouts, backups, or transport channels—and, in containerized workloads, using cgroups to enforce resource isolation boundaries that limit how processes can consume CPU, memory, and I/O, reducing the chance that noisy-neighbor behavior or resource exhaustion disrupts controls protecting CUI, based on the categories of information defined for the program or contract.
The following points are related to protecting CUI across digital and physical media under NIST 800-171:
Control access to media containing CUI
- Restrict physical and logical access so only authorized personnel can view or handle CUI.
- Apply role-based controls to limit exposure of CUI within systems, removable storage, and printed materials.
Identify and label media
- Mark storage devices, documents, and backups to reflect CUI sensitivity and handling rules aligned with agencies with recommended security requirements.
Secure storage and handling
- Encrypt digital storage, secure endpoints, and physically safeguard paper records and removable media.
- Store media in controlled environments to prevent unauthorized duplication or retrieval.
Protect transport and transmission
- Use approved secure channels for moving digital media and enforce custody procedures for physical media.
Sanitize or destroy media before disposal
- Wipe, degauss, shred, or destroy media so data cannot be reconstructed after disposal or reuse.
Control mobile and removable media
- Restrict external drives, personal devices, and portable storage to prevent uncontrolled transfer of CUI.
Who is required to comply with NIST SP 800-171?
Organizations required to comply with NIST SP 800-171 are those that handle Controlled Unclassified Information (CUI) on nonfederal systems as part of U.S. government work or contractual obligations. The requirement is typically driven by federal contracts, regulations, and program mandates tied to safeguarding sensitive government data.
- Federal contractors and subcontractors that store, process, or transmit CUI in nonfederal systems (commonly required via contract clauses such as DFARS 252.204-7012).
- Any nonfederal organization whose systems handle CUI or provide protection for components that handle CUI under a federal agency agreement or contract.
FAQs
- What role does container runtime security play in NIST SP 800-171 compliance?
Runtime security helps detect unauthorized processes, privilege misuse, and data access attempts affecting CUI within containerized workloads.
- How does SBOM support NIST SP 800-171 alignment for containerized systems?
A Software Bill of Materials improves visibility into components handling CUI, enabling risk tracking, vulnerability response, and audit readiness.
- Do container registries fall under the scope of NIST SP 800-171 controls?
Yes. Registries storing images with CUI must enforce access control, logging, encryption, and protection measures consistent with NIST requirements.
- How does zero trust architecture relate to protecting CUI in containers?
Zero trust limits implicit trust, verifies identity continuously, and restricts lateral movement—reducing exposure of CUI across distributed systems.
- What risks arise when CI/CD pipelines handle CUI?
Build pipelines may expose secrets, credentials, and artifacts; they must enforce secure access, integrity checks, and audit logging to protect CUI.
- How do incident response workflows change for containerized CUI environments?
Teams must isolate affected containers, preserve logs, track image provenance, and restore workloads securely without exposing sensitive information.



