ISO 27001 Controls Applied to Kubernetes and Container Security
Securing Kubernetes under ISO 27001 demands more than policies. This article explains ISO 27001 fundamentals, control mapping to Kubernetes and containers, cluster hardening, automation, audits, and compliance tooling, helping teams align operations with risk-driven governance and measurable security outcomes across modern container environments.
What is ISO 27001?
ISO 27001 (formally ISO/IEC 27001) is an international security standard that defines the requirements for establishing, implementing, maintaining, and continually improving an Information Security Management System (ISMS), so an organization can manage information security risks through documented security policies, measurable processes, and risk-based security controls.
ISO 27001 is used to demonstrate compliance and govern how an organization protects sensitive data across environments such as a kubernetes environment, including a kubernetes cluster running containerized applications, where access control, principle of least privilege, and protection of the kubernetes api become auditable control outcomes.
What is the scope of ISO 27001 for Kubernetes and container environments?
The scope of ISO 27001 for Kubernetes and container environments is the documented boundary of your ISMS that states exactly which Kubernetes related assets, processes, and responsibilities are covered, and which are excluded with justification. ISO 27001 requires organizations to define the ISMS scope by considering internal and external context, interested-party requirements, and interfaces and dependencies.
For a Kubernetes and containers scope statement, this typically includes:
- Kubernetes environment and components: the Kubernetes cluster control plane, nodes, networking, and the Kubernetes API access paths used to administer workloads.
- Container lifecycle assets: container image sources, build pipeline steps, registries, and promotion gates used to ship containerized workloads into production.
- Security management processes: the policies and procedures you use to secure Kubernetes, including kubernetes security best practices, configuration standards, and operational checks that reduce security risks.
- Identity and permissions boundary: the access control model applied to clusters and workloads, including least-privilege permissions as a control outcome (a common best practice for limiting blast radius).
- Incident scope: what qualifies as a security incident in your Kubernetes and container environment, and which clusters, namespaces, or workloads fall under your incident response and evidence collection process.
How do ISO 27001 controls apply to Kubernetes and container security?
ISO 27001 controls apply to Kubernetes and container security by turning your iso 27001 compliance program into auditable, risk-based information security controls that govern how you configure, operate, and monitor a kubernetes cluster and its container lifecycle so you can demonstrate iso 27001 compliance and ensure compliance within a defined compliance framework. ISO/IEC 27001 defines ISMS requirements, while its Annex A control set is commonly implemented using detailed guidance from ISO/IEC 27002, with controls grouped into organizational, people, physical, and technological themes.
In Kubernetes terms, that control intent typically maps into four practical areas:
- Governance and policy as controls: You define security policies and operating procedures for cluster ownership, change control, and workload onboarding so implementing security becomes repeatable and reviewable, which is central to achieving iso 27001 compliance.
- Cluster access control and identity: You implement enforceable authorization such as kubernetes role-based access control (kubernetes rbac) to limit administrative and workload permissions, reducing security risks or vulnerabilities that come from excessive privileges and supporting kubernetes compliance evidence. Kubernetes RBAC is designed to regulate access via the Kubernetes API and is a core lever for least-privilege security practices.
- Workload admission and isolation: You apply policy-driven controls to kubernetes pods using pod security and pod security standards to enforce baseline workload hardening, privilege restrictions, and safer defaults across namespaces, which raises the measurable security posture of a secure kubernetes environments program.
- Detection, monitoring, and response: You operationalize runtime security, continuous security, and security monitoring so misconfigurations and security vulnerabilities are detected early and handled through defined security operations processes, making security incident handling and post-incident improvement provable during assessment. Container security guidance such as NIST SP 800-190 also frames controls across the container ecosystem (images, registries, runtimes, orchestration) in a way that aligns with risk-based control implementation.
How do you secure Kubernetes for ISO 27001 compliance?
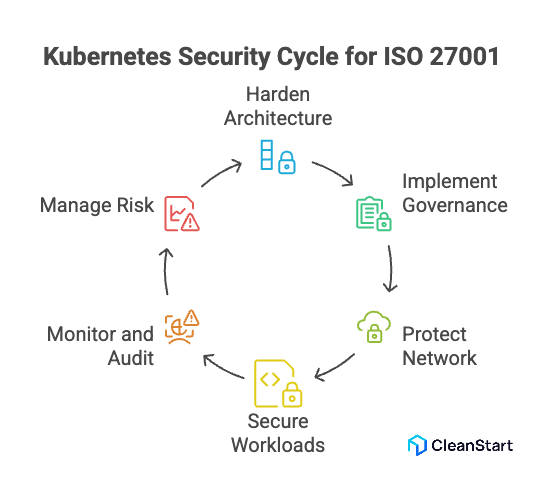
You secure Kubernetes for ISO 27001 compliance by translating ISO 27001 standards and ISO 27001 requirements into enforceable technical and operational security measures across the Kubernetes lifecycle, so the platform consistently protects data, reduces risk, and produces auditable control evidence. In Linux-based Kubernetes, cgroups act as the kernel enforcement layer that constrains pod and container CPU and memory usage, which helps make resource governance measurable and verifiable in audits. ISO 27001 requires risk-based information security standards supported by documented controls, monitoring, and continuous improvement.
In a Kubernetes context, this is implemented through:
- Hardened Kubernetes architecture
Apply secure kubernetes configurations across the kubernetes control plane, worker nodes, and networking to prevent exposure and reduce security misconfigurations. This supports comprehensive security aligned with the iso 27001 framework to define risk treatment and operational safeguards.
- Identity, access, and platform governance
Implement enforceable security controls across clusters, namespaces, and workloads to secure your kubernetes environment and demonstrate a measurable commitment to security during assessment and review cycles.
- Network and cloud protection layers
Apply network security and cloud security controls such as segmentation, encrypted traffic, and environment isolation to protect data flows and strengthen data security in distributed cluster deployments.
- Secure workload lifecycle and development
Integrate secure coding practices, validated deployment pipelines, and hardened runtime policies across the container orchestration workflow so security challenges are addressed before workloads reach production.
- Monitoring, detection, and auditability
Use security tools, security scanning, and continuous logging to detect threats and configuration drift within kubernetes, enabling traceability and a defensible kubernetes audit trail. NIST container security guidance emphasizes continuous monitoring and vulnerability management as essential controls in orchestrated environments.
- Operational risk management and improvement
Apply security strategies and industry best practices to implement iso 27001 across the kubernetes ecosystem, then refine controls through incident reviews and corrective actions so the platform continues to improve kubernetes resilience over time.
A properly secured Kubernetes deployment demonstrates how an organization can comply with iso 27001, maintain control effectiveness, and ensure that security remains embedded in how clusters are configured, operated, and monitored while running production workloads.
How do you automate ISO 27001 and Kubernetes security compliance?
You automate ISO 27001 and Kubernetes security compliance by converting ISMS requirements into “policy as code” and continuous evidence collection, then enforcing those controls at build time and admission time while monitoring drift and producing audit-ready logs. ISO/IEC 27001 defines requirements for an ISMS that is maintained and continually improved, which makes automation a practical way to keep control effectiveness consistent in fast-changing Kubernetes estates.
The following points are related to automating ISO 27001 control implementation and verification in Kubernetes.
- Codify controls as versioned policies
Implement security controls as reusable rules (for example, workload hardening, least privilege, and allowed images) so policy intent stays consistent across clusters and teams, even in a dynamic kubernetes environment.
- Enforce controls at cluster admission to prevent noncompliant changes
Use Kubernetes admission mechanisms to block or validate resources before they are accepted by the API server, so implement security controls happens by default rather than by review. Kubernetes “validating admission policies” are an in-process, declarative alternative to webhooks for enforcing validation rules.
- Shift checks left into CI/CD for fast feedback
Run policy checks against manifests before deploy to catch misconfigurations early and make “define the best practices” enforceable in pipelines, not just documentation. Kyverno’s CLI explicitly supports GitOps-style workflows by checking policy compliance of manifests before they are committed and applied.
- Continuously capture audit evidence from the Kubernetes API
Enable and tune Kubernetes audit logging so every API request produces an auditable event stream for reviews and investigations; audit events are generated in the kube-apiserver and recorded according to an audit policy to supported backends (log files or webhooks).
- Automate detection of drift and policy regressions
Compare live cluster state against the desired, version-controlled baseline to identify new security misconfigurations introduced by emergency changes, operator actions, or tool updates while running a kubernetes platform.
- Automate scanning and runtime signals as continuous compliance checks
Use security tools to continuously evaluate “what is running” versus “what is allowed,” and alert on deviations that create new security exposure; NIST’s container security guidance explicitly covers risks and mitigations across the container ecosystem (images, registries, runtimes, orchestration), which is the same surface area that automation must continuously evaluate.
How do you conduct ISO 27001 audits and assessments for Kubernetes compliance?
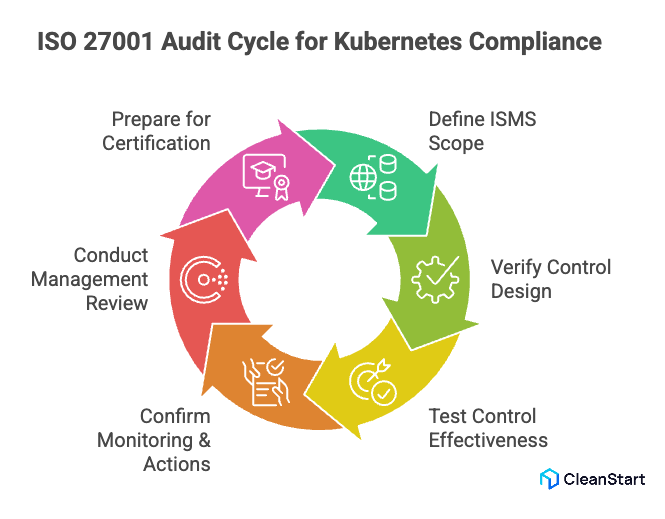
You conduct ISO 27001 audits and assessments for Kubernetes compliance by auditing two things together: the ISMS requirements (scope, risk treatment, governance, performance evaluation) and the Kubernetes control evidence (configuration, access, monitoring, and change history) that proves controls are implemented and effective. ISO 27001 requires planned internal audits and management reviews as part of performance evaluation.
- Define ISMS scope for the Kubernetes setup and dependencies.
- Verify control design meets ISO 27001 requirements for relevant security contexts.
- Test control effectiveness using Kubernetes evidence like audit logs and policy configs.
- Confirm monitoring, nonconformity handling, and corrective actions are documented and executed.
- Conduct management review on Kubernetes compliance posture and changes.
- For certification, prepare for Stage 1 documentation review and Stage 2 implementation testing.
What Kubernetes security features and tools support ISO 27001 compliance?
Kubernetes security features and tools support ISO 27001 compliance by providing enforceable access, workload restriction, network segmentation, and audit evidence that map to risk-based control implementation under an ISMS. ISO 27001 is an international information security standard that defines ISMS requirements.
The following points are related to Kubernetes features and tools that help teams secure their kubernetes and follow when managing it security in a way that supports ISO 27001 audits.
- Kubernetes Role-Based Access Control to enforce least-privilege authorization for API actions.
- Pod Security Standards enforced via Pod Security Admission to restrict pod privilege and hardening baselines.
- Security Contexts to set per-pod and per-container privilege and access settings.
- NetworkPolicies to control allowed pod-to-pod and pod-to-network traffic for network security enforcement.
- Kubernetes Audit Logging to capture API activity as evidence that a voluntary iso 27001 audit identifies and validates.
- Admission controllers to implement preventive guardrails before resources persist in the cluster.
- Kyverno to apply policy-as-code for security best practices and compliance validation in clusters.
- OPA Gatekeeper / OPA admission control to enforce policies on Kubernetes objects during create and update operations.
- Trivy to scan container images and Kubernetes targets for vulnerabilities and misconfigurations.
- Kubescape to scan Kubernetes configurations and security posture across clusters.
What ISO 27001 clauses should be implemented for Kubernetes and container programs?
ISO 27001 clauses implemented for Kubernetes and container programs focus on management system governance and risk-driven control execution across the platform lifecycle. These clauses translate the ISMS into operational safeguards that align Kubernetes operations with applicable security regulations and the organizational framework to define the best risk treatment approach.
The following points are related to ISO 27001 clauses commonly implemented in Kubernetes and container programs.
- Clause Context of the organization
Define scope, dependencies, and risks for clusters, workloads, and container supply chains where kubernetes provides orchestration capabilities that must be governed.
- Clause Leadership
Establish accountability, governance roles, and oversight for platform security and compliance ownership across engineering and operations.
- Clause Planning
Identify and treat risks affecting containerized workloads, cluster access, and data exposure using a risk-based model like iso 27001.
- Clause Support
Maintain competence, awareness, documentation, and operational tooling needed to secure platforms like kubernetes and sustain compliance activities.
- Clause Operation
Implement and operate controls across deployment, change management, workload onboarding, and runtime protection in container programs.
- Clause Performance evaluation
Monitor effectiveness through audits, metrics, reviews, and control validation tied to Kubernetes and container operations.
- Clause Improvement
Apply corrective actions, incident learnings, and control refinements to continuously strengthen security maturity and compliance posture.
FAQs
- What is the difference between ISO 27001 and container security standards?
ISO 27001 is a management framework for risk and governance; container standards focus on technical safeguards across images, runtime, and orchestration.
- Do Kubernetes security controls replace ISO 27001 requirements?
No. Kubernetes controls support implementation; ISO 27001 defines governance, risk management, and audit expectations.
- Can small teams implement ISO 27001 controls in Kubernetes?
Yes. Start with scoped clusters, defined risks, and prioritized controls, then expand coverage gradually.
- How often should Kubernetes environments be reviewed for ISO 27001 readiness?
Regular internal reviews and audits are required, especially after architectural or workload changes.
- Does ISO 27001 require specific Kubernetes tools?
No. It requires effective controls and evidence; organizations choose tools that best enforce and monitor those controls.
- Is certification mandatory to demonstrate Kubernetes security maturity?
No. Certification is optional; organizations can still align operations to ISO 27001 and demonstrate control effectiveness.



