FedRAMP Compliance with Container Security Requirements and Checklist
FedRAMP can feel paperwork-heavy until you map it to real controls. This guide explains what FedRAMP compliance is, who must comply, why it matters, how authorization works, and what documentation is required, then connects it to container security requirements, best practices, hardening, tools, challenges, and checklists.
What Is FedRAMP Compliance?
FedRAMP compliance refers to meeting the security and risk management requirements defined under the Federal Risk and Authorization Management Program, a U.S. government program that standardizes how cloud services are assessed, authorized, and continuously monitored before they can be used by federal agencies.
FedRAMP compliance requires a cloud service provider to implement a defined set of security standards based on NIST 800-53 controls, demonstrate those controls through formal documentation, and undergo an independent security assessment before receiving authorization. The objective is to ensure that federal data is protected under consistent, measurable, and enforceable security requirements.
What Does FedRAMP Stand For?
FedRAMP stands for the Federal Risk and Authorization Management Program.
It is a U.S. government program for information security that standardizes how cloud services are assessed for risk, granted FedRAMP authorization, and kept compliant through continuous monitoring requirements.
Who Must Comply with FedRAMP?
Organizations must comply with FedRAMP if they provide, operate, or manage cloud services used by the United States federal government.
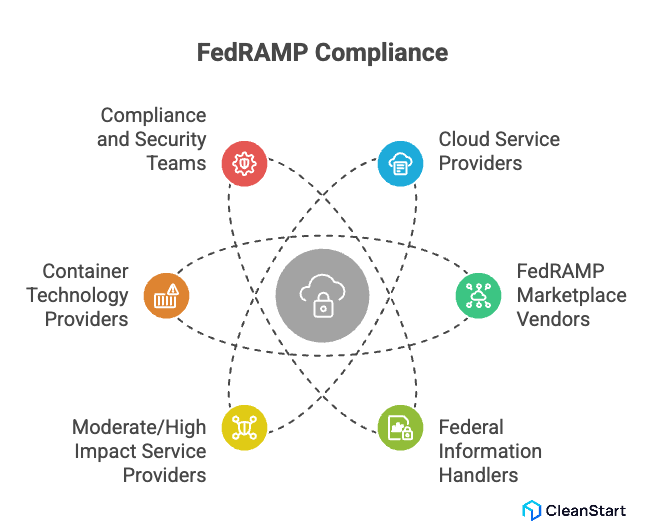
FedRAMP compliance applies to the following entities:
- Cloud service providers: Offering SaaS, PaaS, or IaaS solutions to federal agencies, regardless of deployment model.
- Vendors listed or seeking listing in the FedRAMP Marketplace: Where only FedRAMP authorized services are permitted.
- Organizations handling federal information: That must meet defined fedramp requirements and demonstrate an approved security posture.
- Service providers operating at Moderate or FedRAMP High impact levels: Where rigorous security standards and baseline controls are mandatory.
- Technology providers using container technologies: Where FedRAMP requires container security, defined vulnerability scanning requirements, and enforcement of security controls across container images and runtimes.
- Compliance teams and security teams: Responsible for implementing fedramp controls, maintaining continuous compliance, and supporting the FedRAMP authorization process governed by the FedRAMP PMO and the Joint Authorization Board.
Why Is FedRAMP Compliance Important?
Here’s why it is important:
- It standardizes security and compliance for cloud services used by federal customers by enforcing a standardized approach to security assessment, authorization, and continuous monitoring.
- It reduces duplicated audits across agencies because FedRAMP enables reuse of security assessment results and authorization evidence across the federal government.
- It is a commercial gate for federal work because FedRAMP-authorized services appear in the FedRAMP Marketplace, a searchable database used to identify eligible cloud service offerings.
- It enforces ongoing risk reduction through continuous monitoring requirements, including recurring vulnerability management activities and reporting that preserve the service’s security posture after authorization.
- It matters for containerized environments because FedRAMP defines explicit vulnerability scanning requirements for containers, including the rule that production deployments must use container images scanned within a 30-day vulnerability scanning window.
How Does FedRAMP Reduce Security Risk?
Here’s how it reduces security risk:
- It enforces a standardized set of security controls and assessment criteria, which reduces gaps created by inconsistent security expectations across environments.
- It requires formal security documentation, including a system security plan, so the system boundary, control ownership, and implementation details are explicit and auditable.
- It requires independent validation through a security assessment and a resulting security assessment report, which reduces the chance that control effectiveness is assumed rather than tested.
- It forces remediation discipline through a plan of action and milestones, reducing exposure time by tracking and closing control and vulnerability gaps as part of the authorization lifecycle.
- It reduces operational risk after authorization through FedRAMP continuous monitoring, which requires recurring evidence that controls remain effective and that the security posture has not degraded.
- It reduces exploit risk by mandating recurring vulnerability management and FedRAMP vulnerability scanning practices, including explicit vulnerability scanning requirements for containerized workloads.
- For container environments, it reduces supply chain and deployment risk by requiring that container images are scanned within a 30-day vulnerability scanning window, and by requiring registry and deployment processes to enforce that only compliant images run in production.
What Are FedRAMP Compliance Requirements?
FedRAMP compliance requirements define the mandatory security conditions a cloud service must meet before it can be authorized for use by U.S. federal agencies. These requirements are enforced under the FedRAMP program to ensure consistent protection of federal data across all cloud environments.
Key FedRAMP compliance requirements include:
- Implementation of defined security controls: Based on approved FedRAMP baselines, supported by documented security measures and aligned security policies, with cgroups enforcing resource limits and isolation that prevent noisy-neighbor contention and keep security controls reliable under load.
- Demonstration of compliance requirements through evidence: Including configuration artifacts, audit logs, and technical validation aligned with FedRAMP security expectations.
- Continuous vulnerability management: Requiring routine scanning using approved scanning tools and correlation against a recognized vulnerability database such as the National Vulnerability Database.
- FedRAMP vulnerability scanning requirements: Which mandate that cloud components are assessed on a recurring basis, including a defined 30-day scanning window for production systems.
- Container security requirements: For modern platforms, where container images must be hardened, evaluated through container scanning, and validated before deployment.
- Container registries and orchestration environments: Must enforce that only approved images are deployed, supporting runtime security and preventing unauthorized workloads.
- Automated vulnerability scans: Must be used where possible to maintain continuous visibility and reduce exposure time between discovery and remediation.
- Security sensors should be deployed: To provide insight into the security posture and detect deviations from approved baselines.
- Ongoing compliance operations: Including monitoring, remediation, and reporting, to support maintaining FedRAMP authorization after approval.
What are the Stages of FedRAMP Authorization?
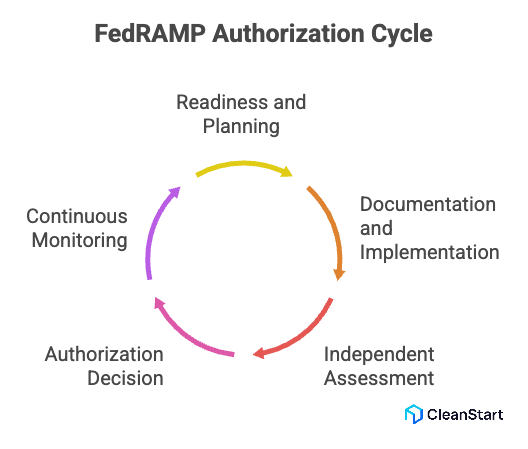
Given below are the stages of FedRAMP authorization:
- Readiness and planning: Define scope, complete the FedRAMP integrated inventory workbook, and align evidence to meet FedRAMP requirements.
- Documentation and implementation: Produce required security documentation and implement controls, including container hardening where a FedRAMP container is in scope, and use a Dockerfile to codify hardening steps such as base image pinning, package minimization, non-root execution, and secure configuration defaults.
- Independent assessment: Validate control effectiveness, including a comprehensive vulnerability review using a vulnerability scanner and required container vulnerability scanning.
- Authorization decision: Authorizing officials review results and approve or require remediation to ensure compliance.
- Continuous monitoring: Maintain the security baseline and maintain FedRAMP compliance through ongoing monitoring and updates.
What Are the Different Types of FedRAMP Authorization?
Given below are the different types of FedRAMP authorization:
What Documentation Is Required for FedRAMP Authorization?
FedRAMP authorization requires a defined set of standardized documents that demonstrate how security controls are implemented, tested, and maintained within the FedRAMP boundary. These documents form the official authorization package reviewed by federal authorizing officials.
The required FedRAMP documentation includes:
- System Security Plan: Defines the system boundary, architecture, data flows, control implementations, and how security responsibilities are assigned within the FedRAMP environment.
- Security Assessment Plan: Describes the testing methodology, scope, and procedures used to evaluate control effectiveness against FedRAMP requirements.
- Security Assessment Report: Provides verified assessment results, detailing which controls passed, failed, or require remediation, and confirms whether the container entrypoint enforces the required startup configuration, fails closed on missing controls, and prevents insecure runtime fallbacks.
- Plan of Action and Milestones: Tracks identified risks, required remediation actions, timelines, and ownership as part of achieving FedRAMP compliance.
- FedRAMP Integrated Inventory Workbook: Documents all in-scope system components that must be monitored and assessed throughout the authorization lifecycle.
- Vulnerability scanning evidence: Demonstrates compliance with the vulnerability scanning requirements document and supports continuous monitoring expectations.
- Security Technical Implementation Guides alignment: Shows how operating systems, platforms, and services follow approved security configuration baselines.
- Container-specific documentation when applicable: If container technologies are used within the FedRAMP boundary, documentation must explain how container orchestration tools are secured, how container must be validated before deployment, and how the components of the container image are protected to maintain a secure container environment.
What Are FedRAMP Container Security Requirements?
FedRAMP container security requirements define how containerized workloads must be secured when they operate within a FedRAMP-authorized cloud environment. These requirements ensure that containers follow the same federal security expectations applied to all in-scope system components.
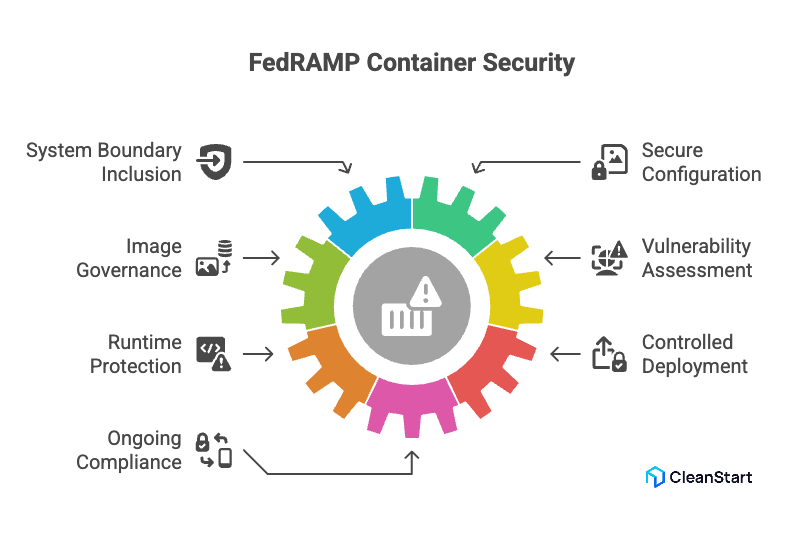
Key FedRAMP container security requirements include:
- Container inclusion within the system boundary: Ensuring containers are explicitly documented and assessed as part of the authorization scope.
- Secure container configuration: Requiring hardened images and controlled runtime settings aligned with federal security baselines.
- Image governance and validation: Where only approved container images are permitted for deployment under the FedRAMP compliance checklist.
- Vulnerability assessment and remediation: Requiring container images and dependencies to be evaluated prior to deployment and during operations, and ensuring the container runtime enforces admission, isolation, and policy controls that prevent unscanned or non-compliant images from executing.
- Runtime protection and monitoring: Ensuring container activity is observable and deviations from approved configurations are detected.
- Controlled deployment processes: Where implementing container workflows must prevent unauthorized images or configurations from entering production. How Should Container Images Be Hardened for FedRAMP? Container images should be hardened for FedRAMP by reducing attack surface, enforcing build integrity, and ensuring every image can be audited, scanned, and controlled throughout its lifecycle. Key hardening practices include:
What Are Container Security Best Practices for FedRAMP Compliance?
Given below are the container security best practices for FedRAMP compliance:
- Define and maintain: The FedRAMP container scope across clusters, registries, CI, and runtimes.
- Standardize on hardened: Minimal base images and enforce immutable image digests in production.
- Scan images: Before deploy and block noncompliant builds using policy gates.
- Allowlist registries and require image: Signing with signature verification at admission.
- Harden runtime defaults: Non-root, least privilege, no privileged containers, restricted capabilities, and use a container registry to store only approved images with signed tags so deployments pull hardened builds instead of unknown variants.
- Enforce isolation and network controls: Namespace boundaries, node segregation when needed, default-deny policies.
- Protect secrets and access: External secret storage, short-lived credentials, least-privilege workload identity.
- Monitor continuously: Audit logs, runtime telemetry, alerting, and evidence retention for compliance.
- Rebuild and patch quickly: Rebuild images on base updates and track remediation with auditable proof.
How Should Container Images Be Hardened for FedRAMP?
Container images should be hardened for FedRAMP by reducing attack surface, enforcing build integrity, and ensuring every image can be audited, scanned, and controlled throughout its lifecycle.
Key hardening practices include:
- Use minimal, approved base images and eliminate unnecessary packages, shells, and utilities.
- Remove default credentials, test files, and unused services from the image.
- Pin exact image versions and digests to prevent untracked changes between builds.
- Run containers as non-root and drop all unnecessary Linux capabilities.
- Configure read-only root filesystems wherever application design allows.
- Separate build and runtime stages using multi-stage builds to exclude compilers and tooling.
- Ensure all components of the container image are documented and traceable for audit review.
- Scan images during build and prior to deployment to verify that only approved images are promoted.
- Rebuild images whenever base layers change to address newly disclosed vulnerabilities.
- Store hardened images only in approved registries with strict access controls and logging.
What Tools Support FedRAMP Container Security?
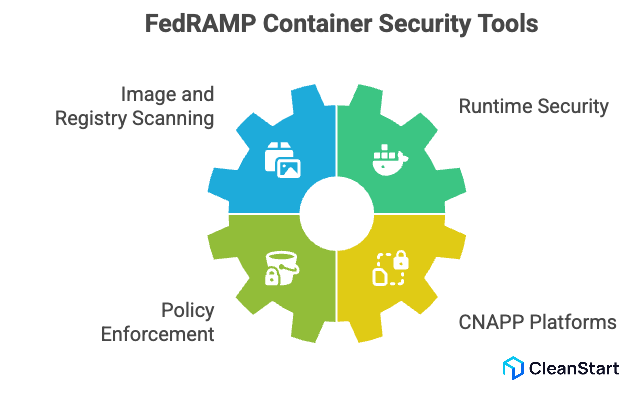
Given below are the tools that support FedRAMP container security:
- Container image and registry scanning tools: These tools perform image scanning, produce auditable findings, and support FedRAMP vulnerability scanning requirements for containers (for example, platforms positioned specifically for FedRAMP container scanning and ConMon reporting).
- Runtime security and workload protection tools: These tools monitor in-cluster behavior and, when scanning in production is needed, support the “independent security sensors deployed alongside production-deployed containers” approach described in FedRAMP guidance.
- Policy enforcement and admission control tools: These tools block noncompliant images from being deployed and enforce container security policies at deploy time, which aligns with FedRAMP’s expectation that automation prevents noncompliant containers from reaching production.
- CNAPP platforms with FedRAMP authorizations: These tools combine container security, vulnerability management, and continuous monitoring workflows for federal use cases (examples publicly claiming FedRAMP High authorization include Aqua CNAPP and Prisma Cloud).
What Are the Common FedRAMP Container Security Challenges?
Given below are the common FedRAMP container security challenges:
- Scope and boundary clarity: Defining what is “in scope” across clusters, registries, CI, and runtimes can be hard to document and defend in audits.
- Ephemeral workloads: Short-lived containers reduce the window to capture logs, telemetry, and proof of control enforcement.
- Image churn and dependency drift: Frequent rebuilds and updates make scan freshness and consistency difficult to maintain.
- Scan coverage at scale: Large image volumes and fast deploy cycles create gaps in vulnerability scanning and remediation tracking.
- Supply chain exposure: Risk increases from base images and third-party components without strong provenance and governance.
- Policy and runtime enforcement: Keeping admission policies, least-privilege access, and runtime visibility consistent across environments is operationally difficult.
- Audit evidence retention: Collecting and retaining usable evidence across scans, logs, and changes is often underestimated.
What Is a FedRAMP Container Security Checklist? And What Does It Include?
A FedRAMP container security checklist is a set of auditable checks used to prove that containerized workloads meet FedRAMP security requirements during authorization and continuous monitoring.
It typically includes:
- Defined Container Scope: Clusters, registries, CI, and runtimes in the FedRAMP boundary
- In Production: Hardened, approved base images and immutable image digests
- Container Image Scanning: Before deploy and on a recurring schedule, with tracked remediation
- Registry Controls: Allowlists, access control, logging, and blocked unapproved images
- Runtime Hardening: Non-root, least privilege, no privileged containers, restricted capabilities
- By Policy: Network segmentation and workload isolation enforced
- Secrets Handling: It prevents credentials in images and restricts access
- Monitoring and Audit Evidence: Logs, alerts, and retained proof of control enforcement
FAQs:
- Does FedRAMP Require Container Images to be Signed?
FedRAMP does not mandate image signing explicitly, but signing is commonly used to demonstrate image integrity and supply chain control.
- Can Open-Source Container Images be Used in FedRAMP Systems?
Yes, but they must be hardened, scanned, documented, and approved before use within the FedRAMP boundary.
- Are Kubernetes Managed Services Automatically FedRAMP Compliant?
No. The managed service may be authorized, but customer workloads and configurations remain the provider’s responsibility.
- How Often Must Container Images Be Rebuilt for FedRAMP?
Images should be rebuilt whenever base layers change or new vulnerabilities are disclosed to maintain scan validity.
- Can FedRAMP Container Scanning be Automated?
Yes. Automated scanning is encouraged to maintain continuous compliance and reduce remediation delays.
- Does FedRAMP Require Runtime Monitoring for Containers?
FedRAMP expects continuous monitoring; runtime visibility is commonly used to demonstrate ongoing control effectiveness.



