HIPAA Cloud Compliance for Containerized Healthcare Applications
Running containerized healthcare apps in the cloud is fast, but HIPAA makes it unforgiving. This guide covers what HIPAA is, who it applies to, noncompliance penalties, what makes a cloud provider HIPAA compliant, cloud best practices, compliant cloud architecture, common cloud challenges, and how containers and Kubernetes affect HIPAA.
What is HIPAA?
HIPAA, the Health Insurance Portability and Accountability Act, is a United States federal law and regulatory framework that sets national standards for protecting individuals’ health information, including PHI (protected health information), and reducing unauthorized access or disclosure by organizations that handle it.
HIPAA compliance is achieved by meeting HIPAA requirements under key HIPAA rules, especially by implementing container security controls that reduce ePHI exposure in containerized workloads through hardened images, least-privilege access, and auditable runtime enforcement.
- Privacy Rule: Defines what protected health information is, who is covered, and when PHI can be used or disclosed.
- Security Rule: Requires administrative, physical, and technical security controls to protect electronic PHI (ePHI), including controls around access control and security safeguards.
When healthcare organizations use cloud services (including public cloud) from a cloud provider such as Google Cloud, HIPAA still applies to PHI handled in cloud infrastructure (for example, cloud storage), and the regulated organization remains responsible for implementing and operating the required cloud security measures (for example, encryption, audit log evidence, and controlled access to PHI) under a shared responsibility model.
Does HIPAA apply to healthcare applications and software vendors?
Yes, but not automatically.
HIPAA applies to healthcare applications and software vendors only when the vendor is a HIPAA-covered entity or, more commonly, a business associate that creates, receives, maintains, or transmits PHI on behalf of a covered entity (for example, building, hosting, operating, or supporting an app that handles PHI for a provider or health plan).
If a software vendor’s app is consumer-directed and the vendor is not acting as a covered entity or business associate, then HIPAA generally does not apply to that vendor, even if the app processes health data.
For vendors that must comply with HIPAA (business associates), HIPAA obligations typically flow from the Security Rule and require them to implement HIPAA security safeguards and operate a hipaa-compliant environment for PHI, which in practice often includes cloud compliance controls such as properly configuring systems, restricting access, encrypting healthcare data, and managing vulnerability risk in cloud or containerized deployments.
Separately, some health apps and similar products not covered by HIPAA may still have breach notification obligations under the Federal Trade Commission Health Breach Notification Rule.
Who does HIPAA apply to?
HIPAA applies to two groups: covered entities and their business associates.
HIPAA covered entities are:
- Healthcare providers (only if they transmit health information electronically in standard transactions)
- Health plans
- Healthcare clearinghouses
HIPAA business associates are vendors that perform services for a covered entity and, in doing so, create, receive, maintain, or transmit PHI, including a cloud service provider or other cloud solutions vendor that handles PHI in the cloud (for example via an API into a cloud environment). If you run containerized applications that process PHI using modern cloud environments or public cloud services, you still must comply with the HIPAA Security Rule and related privacy and security obligations, and you typically document that relationship through a business associate agreement (BAA) to demonstrate and maintain a secure, hipaa compliant compliance posture, including enforcing resource isolation with cgroups, which constrain CPU and memory usage per container to reduce noisy-neighbor risk and support stable, auditable workload behavior.
What are the costs and penalties of HIPAA noncompliance?
HIPAA noncompliance costs fall into regulatory penalties, enforcement remediation, and downstream business impact.
Civil monetary penalties for HIPAA violations
- For HIPAA privacy and security violations assessed on or after January 28, 2026 (and for violations occurring on or after November 2, 2015), inflation-adjusted penalty amounts include minimum per-violation penalties that scale by culpability (from $145 to $73,011).
- The maximum per violation amount is $73,011 for most tiers. For “willful neglect and not timely corrected,” the maximum can reach $2,190,294.
- The calendar-year penalty cap for all violations of an identical HIPAA provision is $2,190,294 (based on the same inflation adjustment).
- OCR has also described enforcement discretion annual caps (not inflation-indexed in that summary): $25,000 (no knowledge), $100,000 (reasonable cause), $250,000 (willful neglect corrected), $1,500,000 (willful neglect not corrected).
Corrective action plans and multi-year oversight
- OCR commonly requires a corrective action plan (policy changes, risk analysis remediation, procedures, and ongoing reporting) that creates direct compliance cost and operational overhead beyond the dollar payment, and it often forces engineering teams to standardize build controls through a Dockerfile, which defines the container image build steps and helps enforce repeatable, auditable configuration defaults.
Criminal penalties for wrongful disclosure
- Wrongful disclosure of protected health information can trigger criminal penalties, including up to $50,000 and 1 year imprisonment, up to $100,000 and 5 years if done under false pretenses, and up to $250,000 and 10 years if done with intent to sell, transfer, or use for personal gain or malicious harm.
Investigation, breach response, and “security and privacy” remediation costs
- Even when OCR resolves a case via settlement, organizations typically incur costs for incident response, forensic work, legal support, and rebuilding security responsibilities such as risk analysis, access safeguards, and monitoring to prevent unauthorized access to PHI, including hardening the container entrypoint, which controls the first process that starts in a container and can enforce safer defaults like dropping privileges, validating configuration, and failing closed when security requirements are missing.
Ongoing enforcement and demonstrated compliance costs
- OCR reports enforcement outcomes as a mix of settlements and civil money penalties; as of November 21, 2024, OCR reported 152 resolution cases with settlements or civil money penalties totaling $144,878,972 (a signal of the financial scale of enforcement in aggregate).
Cloud-related drivers of noncompliance cost
- In HIPAA cloud contexts, costs frequently compound when cloud misconfigurations or weak controls across cloud workloads create reportable exposure of PHI, forcing expensive remediation to re-establish “secure and compliant” operations and evidence for audits, especially when container orchestration platforms automate scheduling, scaling, and networking of containers and can rapidly propagate a single misconfiguration across many replicas and namespaces.
What makes a cloud provider HIPAA compliant?
A cloud provider is considered “HIPAA compliant” in practice when it can legally act as a HIPAA business associate for your use case and supports the controls and contracting needed to protect ePHI under HIPAA regulations.
- It will sign a HIPAA Business Associate Agreement
- It clearly defines shared responsibility for compliance
- It provides “HIPAA-eligible” or “covered” cloud services under the BAA
- It supports HIPAA security rule aligned technical capabilities
- It enables evidence and compliance monitoring
What are HIPAA cloud compliance best practices?
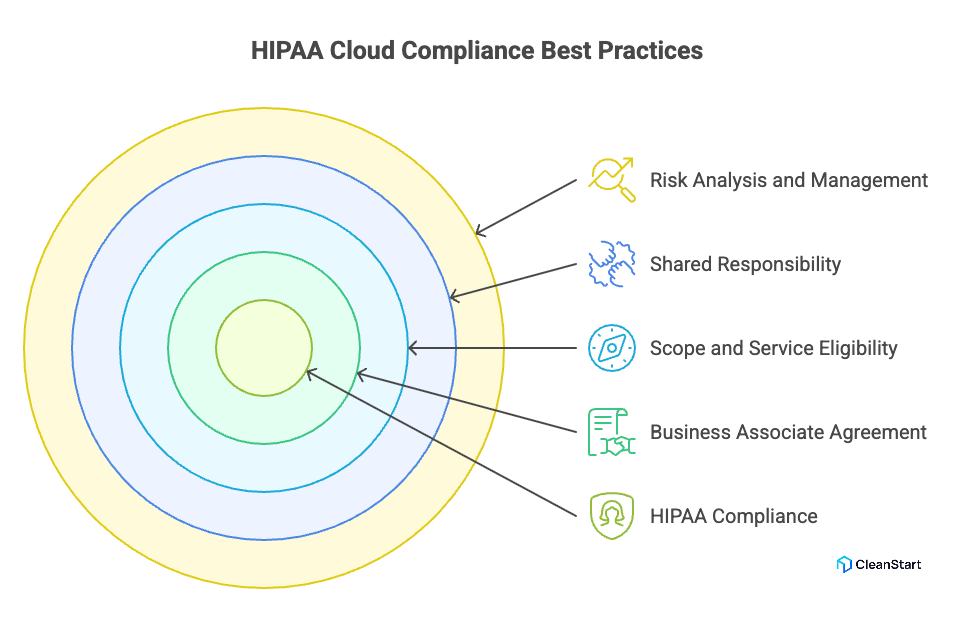
HIPAA cloud compliance best practices are the operational and technical steps that help you meet HIPAA Security Rule and Privacy Rule obligations while handling ePHI in cloud computing.
- Execute a HIPAA Business Associate Agreement with the cloud provider before any use of cloud services that create, receive, maintain, or transmit ePHI, and require an SBOM that enumerates the software components in your workloads so you can trace vulnerable dependencies and produce auditable evidence during compliance reviews.
- Define scope and service eligibility: use only the cloud provider services covered under the BAA and document which cloud data flows contain PHI.
- Apply shared responsibility explicitly: treat “HIPAA-compliant cloud” as a joint outcome where the provider secures underlying cloud infrastructure and you implement configuration and security controls for your workloads.
- Perform a Security Rule risk analysis and risk management cycle to identify and reduce risks and vulnerabilities to ePHI in the cloud environment.
- Implement strong access control and least privilege for all access to PHI, including workforce identities, service accounts, and administrative paths.
- Encrypt ePHI in transit and at rest and manage keys so encryption meaningfully reduces exposure if cloud data is accessed improperly.
- Enable audit controls and retain audit evidence: centralize audit logs for access to ePHI, administrative actions, and security events to support an audit and investigations.
- Harden configurations to prevent cloud misconfigurations that expose ePHI, and continuously validate settings against your compliance requirements.
- Run continuous compliance monitoring for identity, storage, network, and logging controls to maintain HIPAA compliance in the cloud over time.
- Maintain contingency protections (backup, recovery, and tested restore procedures) to preserve availability of ePHI and demonstrate compliance posture under incident conditions.
- If workloads are containerized, treat image and runtime security as part of cloud compliance by reducing vulnerability exposure through controlled build and deployment practices that support secure and compliant operations.
- Use the provider’s HIPAA compliance guidance for implementation details (for example, Google Cloud Platform’s HIPAA documentation) to align your controls with the provider’s covered services and responsibilities.
What does a HIPAA compliant cloud architecture look like?
A HIPAA compliant cloud architecture is a cloud computing design that protects ePHI (personal health information) by combining a signed BAA with the cloud provider, clearly assigned security responsibilities, and Security Rule safeguards across identity, data, network, monitoring, and recovery.
- A HIPAA-compliant cloud foundation starts with a BAA and a defined scope of covered services (for example, specific Google Cloud Platform services).
- The architecture implements Security Rule security requirements through administrative and technical safeguards, including risk analysis, risk management, and technical controls, and it uses a hardened container image that ships with reduced packages and secure defaults to lower exploitable exposure in production.
- The design enforces strong identity and authorization paths so only approved roles and workloads have access to ePHI, supporting privacy and security rules and minimizing exposure.
- The architecture protects data using encryption and integrity protections for ePHI in transit and at rest, aligned to technical safeguard requirements.
- The architecture includes centralized monitoring and audit evidence generation (logging, audit controls, retention) so you can demonstrate compliance and support investigations.
- The architecture includes contingency protections (backup, recovery planning, and tested procedures) to maintain availability and operational resilience.
- In modern environments, the architecture also treats container images and runtime boundaries as part of maintaining compliance when workloads are containerized, because the Security Rule applies to all ePHI handling systems regardless of deployment model.
What are the main HIPAA cloud compliance challenges?
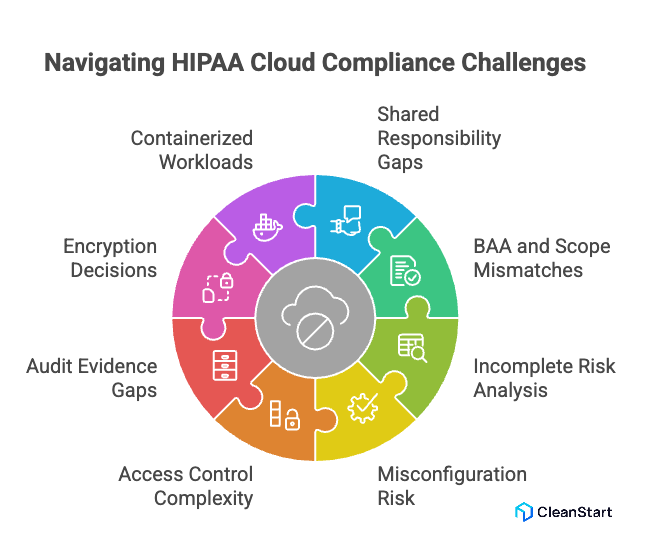
The following points are related to the main HIPAA cloud compliance challenges.
- Shared responsibility gaps: HIPAA compliance in the cloud fails when teams assume the cloud provider “covers HIPAA,” but the customer still must implement and operate required safeguards for ePHI in its own environment.
- BAA and scope mismatches: A missing BAA, or using cloud services outside the BAA scope, breaks the legal and operational basis for handling ePHI with that provider.
- Risk analysis that is incomplete or outdated: HIPAA requires an accurate and thorough assessment of risks and vulnerabilities to ePHI; cloud change velocity makes this easy to underperform without continuous review, especially when teams adopt distroless container images, which remove the OS shell and package managers to shrink the attack surface and change what vulnerabilities and controls must be assessed.
- Misconfiguration risk at scale: Cloud compliance challenges often come from identity, network, and storage misconfigurations that expand access paths and weaken security controls intended to prevent improper exposure of ePHI.
- Access control complexity across identities and services: Enforcing least privilege consistently across human admins, service accounts, and third-party integrations is difficult, and weak access controls undermine Security Rule technical safeguards.
- Audit evidence and logging gaps: HIPAA requires audit controls; in cloud environments, missing, fragmented, or short-retained logs make it hard to prove what happened and to support investigations.
- Encryption decisions that are not defensible: Encryption is addressable (not automatic), which creates a recurring challenge: teams must implement it or document an equivalent, reasonable alternative aligned to the risk analysis.
- Containerized workloads increase the control surface: When cloud workloads are containerized, teams must maintain compliance across image, runtime, and orchestration layers, and missed controls become repeatable failure modes.
How do containers impact HIPAA compliance?
Containers do not change HIPAA obligations, but they change how you implement and prove security and compliance for ePHI because the HIPAA Security Rule applies to the systems that store, process, or transmit ePHI regardless of deployment model.
Containers impact HIPAA compliance for containers in these concrete ways:
- Expanded control surface: ePHI protection depends on controls across the container image, container runtime, host OS, and orchestrator, not only the application.
- Shared-kernel risk model: multiple workloads share the host kernel, so isolation and runtime hardening become part of the compliance needs for confidentiality and integrity.
- Image supply chain becomes compliance-relevant: base images, dependencies, and build pipelines can introduce weaknesses that must be managed as part of security best practices for regulated workloads.
- Ephemeral infrastructure complicates evidence: short-lived containers and auto-scaling increase the importance of centralized logging and repeatable configuration to support auditability and continuous HIPAA posture.
- Operational responsibility stays with the regulated entity: even in cloud, using containers does not shift HIPAA responsibility to the provider; compliance depends on how you configure and operate your environment over time.
How do you secure container images for HIPAA compliance?
To secure container images in a way that supports achieving HIPAA compliance in modern, containerized systems, you implement controls that protect ePHI confidentiality, integrity, and availability under the HIPAA Security Rule, then preserve evidence for audits.
- Control which images can run by allowing only approved registries and approved images, and blocking untrusted sources.
- Scan images before deployment and apply policy gates that prevent running images above your defined risk threshold, because known vulnerabilities in image components increase exposure risk.
- Cryptographically sign images and verify signatures at deploy time to protect image integrity and reduce supply chain tampering risk.
- Minimize image contents (small base images, remove unused packages and tools) to reduce the exploitable surface area and simplify ongoing remediation, because smaller docker images contain fewer installed components, which reduces vulnerability count and shortens patch and rebuild cycles.
- Enforce strict access control to image build and registry operations (who can build, sign, push, pull, and promote images) to reduce unauthorized changes.
- Keep secrets out of images and ensure builds do not embed credentials, because baked-in secrets create durable compromise paths.
- Rebuild and patch images on a defined cadence and after high-risk findings so remediation is applied consistently across deployments.
- Maintain audit evidence for image provenance (build source, signer identity, scan results, promotion approvals) and retain audit log records to support audits and incident investigations as part of ensuring compliance.
How do you set up a HIPAA compliant Kubernetes cluster?
To set up a HIPAA compliant Kubernetes cluster, you build a Kubernetes environment that can protect ePHI under the HIPAA Security Rule and operate it with auditable controls, using only services covered by a signed BAA with a cloud provider.
- Confirm the cloud provider is HIPAA eligible for your use case by executing a BAA and limiting workloads to the specific cloud services covered under that BAA. This is where HIPAA compliance starts for any specific cloud deployment that will store or process ePHI.
- Perform and document a Security Rule risk analysis for the Kubernetes stack (cluster, nodes, networking, storage, CI/CD, registries, logging) and implement risk management actions to reduce risks to a reasonable and appropriate level.
- Implement strong identity and access control for the cluster using least privilege for administrators and workloads, so only authorized identities can access cluster functions and any path to ePHI.
- Segment network paths for workloads so only required service-to-service communication is allowed, and isolate ePHI-handling components from non-PHI components at the network layer.
- Encrypt ePHI in transit and at rest and manage keys in a controlled way, because transmission security and integrity protections are part of HIPAA technical safeguards.
- Secure secrets and workload configuration so credentials, tokens, and keys are not embedded in images or manifests, and access is restricted to the minimal set of pods and operators, and enforce container scanning to detect hardcoded secrets, exposed credentials, and risky configurations before deployment.
- Harden container image intake and deployment by scanning images before deploy, controlling which registries and images can run, and applying policy gates so high-risk images are blocked from production. This is a practical HIPAA compliance feature for preventing repeatable exposure paths.
- Enable audit controls and centralized audit logs for Kubernetes API activity, cluster admin actions, and access paths that can touch ePHI, and retain logs long enough to support investigations and audits.
- Establish continuous monitoring for misconfiguration and drift across identities, network controls, logging, and storage policies, because Kubernetes clusters change frequently and compliance depends on how the environment is operated over time.
- Implement contingency protections (backup and restore procedures and testing) for workloads and data that include ePHI, aligned to Security Rule expectations for availability planning.
FAQs
1. Do all healthcare apps automatically fall under HIPAA?
No. HIPAA applies when the app is operated by a covered entity or a business associate handling ePHI for a covered entity, not simply because the app is “health-related.”
2. If a cloud provider signs a BAA, does that make my deployment HIPAA-compliant?
No. A BAA enables the provider relationship, but you still must implement and operate the required safeguards in your environment to comply.
3. When does the HIPAA breach notification clock start, and what is the deadline?
It starts when the breach is discovered, and notifications must be made without unreasonable delay and no later than 60 days in most cases; reporting to HHS differs based on whether fewer than 500 individuals are affected.
4. What is the “minimum necessary” standard, and does it matter for cloud access design?
Yes. The Privacy Rule requires reasonable efforts to limit uses, disclosures, and requests for PHI to the minimum necessary for the purpose.
5. Can we use de-identified data instead of PHI for analytics in the cloud?
Yes, if you de-identify data using a HIPAA-recognized method such as Safe Harbor or Expert Determination under HHS guidance.
6. Do patients have a right to access their PHI held by providers, and what is the response timeline?
Yes. After a written request, a covered entity generally has 30 days to provide the requested PHI (with a limited extension option).



