PCI DSS 4.0 Compliance for Containerized Payment Workloads
If your payment workloads run in containers, PCI DSS 4.0 is no longer just a checkbox. This article explains what PCI DSS 4.0 compliance means, who must comply, the core requirements, how the standard applies to cloud and containers, meeting requirements for containerized payment workloads, risk-based continuous compliance, stronger identity and access controls, common container adoption challenges, and what changed from earlier versions.
What Is PCI DSS 4.0 Compliance?
PCI DSS 4.0 compliance means meeting the Payment Card Industry Data Security Standard requirements issued by the PCI Security Standards Council for any environment that stores, processes, or transmits cardholder data (the cardholder data environment, or CDE) as part of payment processing and credit card transactions.
Who Must Comply With PCI DSS 4.0?
Any organization that stores, processes, or transmits cardholder data as part of credit card transactions must comply with PCI DSS 4.0, regardless of size, geography, or deployment model. Compliance obligations extend across the full payment data lifecycle, from ingestion to storage, transmission, and deletion, and apply equally to traditional and modern environments.
PCI DSS 4.0 compliance is required for the following entities:
- Merchants and service providers that directly handle cardholder data and must demonstrate regulatory compliance through a PCI audit or a validated SAQ, depending on transaction volume and scope, including evidence that their container orchestration platform enforces scoped deployment, segmentation, and access policies so only authorized workloads can reach payment systems and cardholder data.
- Organizations deploying containerized workloads, including cloud-native applications running on a cloud platform, Kubernetes, or managed clusters, when those workloads are part of the cardholder data environment and operate at build time, runtime, or during deployment.
- Third-party service providers that support payment processing functions such as hosting, application services, logging, monitoring, or vulnerability management, under the shared responsibility model defined by PCI DSS.
- Cloud service customers who remain accountable for PCI controls related to access control, authentication, identity and access, encryption, monitoring, and remediation, even when infrastructure is managed by a provider.
- Organizations undergoing formal validation, where compliance is assessed by an auditor or assessor, often a QSA, and documented through an attestation of compliance.
- Businesses preparing for future-dated requirements, where PCI DSS 4.0 expectations fully apply for assessments conducted in 2025, including stronger access controls, risk-based security validation, and prevention of unauthorized access.
What Are the Core PCI DSS Requirements Under Version 4.0?
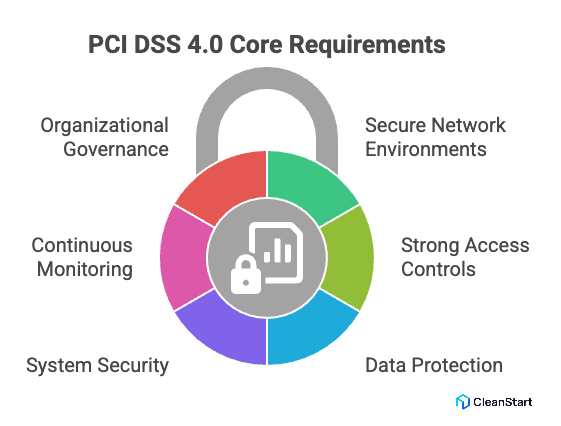
The core PCI DSS requirements under version 4.0 define the mandatory security controls that organizations must implement to protect cardholder data across systems involved in payment processing. These requirements apply uniformly to merchants and service providers supporting credit card companies, regardless of technology stack or scale.
The core requirements focus on the following areas:
- Establish and maintain secure network environments
Organizations must deploy and manage network security controls that limit exposure of cardholder data and prevent unauthorized access.
- Apply strong access and authentication mechanisms
PCI DSS 4.0 emphasizes strong access controls, including role-based access, secure authentication, and restriction of privileges to what is strictly necessary.
- Protect cardholder data at rest and in transit
Sensitive data must be rendered unreadable using approved cryptography to ensure data confidentiality throughout its lifecycle.
- Maintain secure systems and applications
Systems handling payment data must be securely configured, regularly updated, and protected against known vulnerabilities through qualified security practices.
- Continuously monitor and test security controls
Logging, monitoring, and testing are required to detect anomalies, validate control effectiveness, and support audit and investigation activities.
- Support organizational security governance and readiness
Policies, procedures, and accountability structures must be defined to demonstrate ongoing compliance readiness and support formal assessments.
Under PCI DSS 4.0, these requirements are assessed based on whether they achieve the intended security outcome, rather than whether they follow a single prescribed method. This shift allows flexibility while preserving enforceability during audits and formal validation, including evidence that each container image build embeds the required controls (for example, hardened packages and secure configurations) that carry into runtime
How Does PCI DSS 4.0 Apply to Cloud and Container Environments?
PCI DSS 4.0 applies to cloud and container environments by extending PCI DSS compliance obligations to modern, shared, and dynamic infrastructures while preserving the core objective of protecting credit card information. The Payment Card Industry Security Standards defined by the PCI Security Standards Council are technology-agnostic, meaning the version of the PCI DSS applies equally to on-premises systems, cloud environments, and containerized environments.
Key application principles include:
- Shared responsibility model enforcement
Under cloud PCI expectations, responsibility for PCI compliance is split between the cloud provider and the customer. Providers secure the underlying infrastructure, while customers remain accountable for access to sensitive systems, cloud data, identity configuration, and application-level controls required to achieve compliance.
- Scope definition for containerized environments
Any container, node, or cluster that processes or has access to credit card information falls within PCI scope. This includes build pipelines, registries, orchestration layers, and runtime components supporting cloud-native workloads.
- Control validation aligned to PCI DSS 4.0 requirements
Organizations must demonstrate effective strong access control measures, authentication, encryption, and segmentation across container platforms, even as containers scale or redeploy dynamically.
- Runtime security and monitoring
PCI DSS 4.0 introduces stronger expectations for detection and response, including continuous monitoring of sensitive resources. Controls such as file integrity monitoring and runtime visibility help detect unauthorized changes in ephemeral container environments.
- Assessment and validation
Compliance is validated through a PCI DSS assessment conducted by a Qualified Security Assessor, with results documented in a PCI DSS attestation of compliance. This applies equally under PCI DSS 4.0.1 compliance, which clarifies intent without introducing new requirements.
How Can Containerized Payment Workloads Meet PCI DSS 4.0 Requirements?
Containerized payment workloads meet PCI DSS 4.0 requirements by translating the standard’s outcome-based security requirements into controls that function consistently across dynamic, ephemeral environments. The Card Industry Security Standards Council defines PCI DSS as technology-agnostic, so the same compliance expectations apply to running containers as they do to traditional systems, regardless of the versions of the standard in use.
Key requirements are met by ensuring the following:
- Controlled scope within container platforms
Only containers, services, and namespaces that handle payment functions are included in scope, particularly when deployed on a managed Kubernetes service, reducing exposure while maintaining compliance coverage.
- Consistent enforcement of security controls
PCI DSS 4.0 expects access restrictions, segmentation, and configuration controls to remain effective throughout the container lifecycle, including build, deployment, and runtime stages.
- Strong identity and access governance
Access to containerized payment workloads must be tightly managed using authenticated identities, role-based permissions, and least-privilege principles that remain enforceable as containers scale or restart.
- Runtime visibility and change detection
Because containers are short-lived, PCI DSS 4.0 emphasizes continuous visibility into active workloads to detect unauthorized changes or behavior that could impact payment data security.
- Alignment with PCI DSS 4.0 outcomes
What’s new in PCI DSS is the focus on proving that controls achieve their intended outcome, not merely that they exist. Container security implementations must therefore demonstrate effectiveness during assessment, regardless of deployment architecture.
Why Does PCI DSS 4.0 Emphasize Continuous and Risk-Based Compliance?
PCI DSS 4.0 emphasizes continuous and risk-based compliance because payment environments change too quickly for point-in-time controls to remain reliable, and because different organizations face different threat exposures even when they process similar payment volumes. PCI DSS 4.0, first released in 2022, shifts the standard toward validating that controls continuously achieve intended security outcomes, not just that they existed during an audit window, including whether container isolation controls such as cgroups enforce resource boundaries that reduce unauthorized process behavior and limit blast radius at runtime.
It does this in two concrete ways:
- Future-dated requirements transition to mandatory controls
Many new requirements were labeled “best practice” initially, then became effective later, which reinforces the expectation that organizations mature controls over time and operate them continuously rather than treating compliance as an annual project.
- Targeted Risk Analysis enables justified, risk-based control operation
PCI DSS 4.0 introduces Targeted Risk Analysis (TRA) so entities can evaluate their specific risks and determine security impact and, where allowed, control frequency or method based on documented risk, instead of using a one-size-fits-all cadence.
How Does PCI DSS 4.0 Strengthen Identity and Access Controls?
PCI DSS 4.0 strengthens identity and access controls by raising the bar from “unique IDs and passwords” to “verified identity, stronger authentication, and continuously controlled access” across every system component that can reach the cardholder data environment. This shift aligns the standard with modern attack patterns (credential theft, session abuse, and over-privileged access) and makes identity a primary control for security and compliance outcomes.
Concretely, PCI DSS 4.0 strengthens identity and access in these ways:
- It expands multi-factor authentication expectations so access into the cardholder data environment is protected by MFA as future-dated requirements come fully into effect, reducing the risk of unauthorized access from compromised credentials, and it expects the Dockerfile build definition to avoid hardcoding secrets so authentication factors and access tokens are provisioned securely at runtime rather than embedded in images.
- It tightens what “multi-factor authentication” means operationally, including the expectation that factors are independent and implemented in a way that prevents bypass or misuse.
- It reinforces least privilege and business-need access by requiring access rights to be explicitly limited to what job responsibilities require, which reduces lateral movement and the blast radius of a compromised account.
- It clarifies intent and guidance in PCI DSS 4.0.1 without adding new requirements, which affects how organizations interpret and evidence identity and authentication controls during assessments.
What Are the Common Challenges in Adopting PCI DSS 4.0 for Containers?
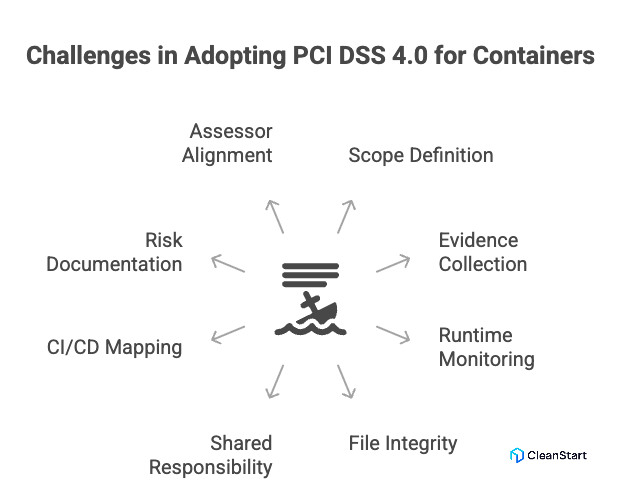
The most common challenges in adopting PCI DSS 4.0 for containers come from the mismatch between PCI evidence expectations and the dynamic nature of container platforms.
- Defining and defending PCI scope in a fast-changing environment
Containers, pods, and services scale and redeploy continuously, which makes it harder to prove where the cardholder data environment boundaries start and end, and whether segmentation is consistently effective.
- In Kubernetes and service-mesh architectures, segmentation is implemented through policies and overlays rather than fixed network zones, and assessors still require clear evidence that segmentation prevents scope bleed, including proof that the container entrypoint startup command does not bypass enforced network policies by launching sidecar-disabled processes or initiating direct egress paths outside the intended segment.
- Evidence collection for ephemeral workloads
Short-lived containers can terminate before logs, alerts, or forensic artifacts are preserved, creating gaps in audit evidence for monitoring, access tracking, and change detection.
- Logging, monitoring, and response coverage at runtime
PCI DSS 4.0’s stronger expectations for ongoing detection and response require real-time visibility into container runtime activity, not just host-level telemetry.
- File integrity monitoring in container contexts
Traditional file integrity monitoring approaches often assume stable hosts and filesystems; containers introduce layered images, immutable patterns, and rapid redeployments that complicate what to monitor and how to baseline changes.
- Shared responsibility ambiguity across cloud, platform, and app layers
Teams often over-assume what the cloud provider “covers,” while PCI DSS still expects the entity to validate responsibilities, scope, and control operation end-to-end. This is a frequent source of audit findings.
- Mapping PCI controls to CI/CD and image supply chain
Container builds introduce new control points (base images, registries, signing, scanning, deployment gates). Organizations struggle to show consistent control enforcement from build to runtime.
- Risk-based documentation expectations under PCI DSS 4.0
PCI DSS 4.0 introduces targeted risk analysis requirements in specific cases; many teams fail on documentation quality, review cadence, or justification rigor when using flexible approaches.
- Assessor alignment and consistency
Containerized implementations vary widely, and audit outcomes often depend on whether evidence is presented in a form a QSA can validate against PCI DSS intent and testing procedures.
What is the difference between PCI DSS 4.0 and earlier versions?
FAQs
1. Does PCI DSS 4.0 require changes to container build pipelines?
Yes. PCI DSS 4.0 expects security controls to be enforced across the full workload lifecycle, which includes container image builds, dependency management, and deployment pipelines.
2. Are container images themselves considered part of PCI scope?
Container images are in scope if they are used to deploy workloads that store, process, or transmit cardholder data, or if they directly influence the security posture of those workloads.
3. How does PCI DSS 4.0 affect DevOps and platform teams?
PCI DSS 4.0 shifts responsibility earlier into the delivery lifecycle, requiring DevOps and platform teams to prove that controls remain effective beyond deployment and into runtime.
4. Can PCI DSS 4.0 controls be automated for container environments?
Yes. Many PCI DSS 4.0 requirements support automation, provided organizations can demonstrate consistent control operation and produce assessor-verifiable evidence.
5. Does PCI DSS 4.0 mandate specific container security tools?
No. The standard is outcome-based. Organizations may choose their own tools as long as they can prove the required security outcomes are achieved.
6. How early should organizations prepare for PCI DSS 4.0 container compliance?
Preparation should begin well before assessment cycles, as container-specific evidence, risk analysis, and runtime controls take time to mature and validate.



