Software Supply Chain Security: Definition, Components, Best Practices, Attacks and Risks
Software supply chain security protects the code, dependencies, build pipeline, and release process that deliver software. This article covers how supply chain attacks exploit trusted update paths, the stages of the software supply chain, common risks, real-world examples, and practical controls including SBOM-based traceability, key frameworks, tool selection, and metrics.
What is software supply chain security?
Software supply chain security is the set of controls and processes used to protect software supply chains from tampering, hidden vulnerabilities, and unauthorized changes across the software development lifecycle, from code creation to build, release, and deployment. It focuses on keeping software components and every software artifact (for example, a signed container with container image pushed to a registry or a compiled binary published to an artifact repository) authentic, traceable, and free from known security risks.
What are the key components?
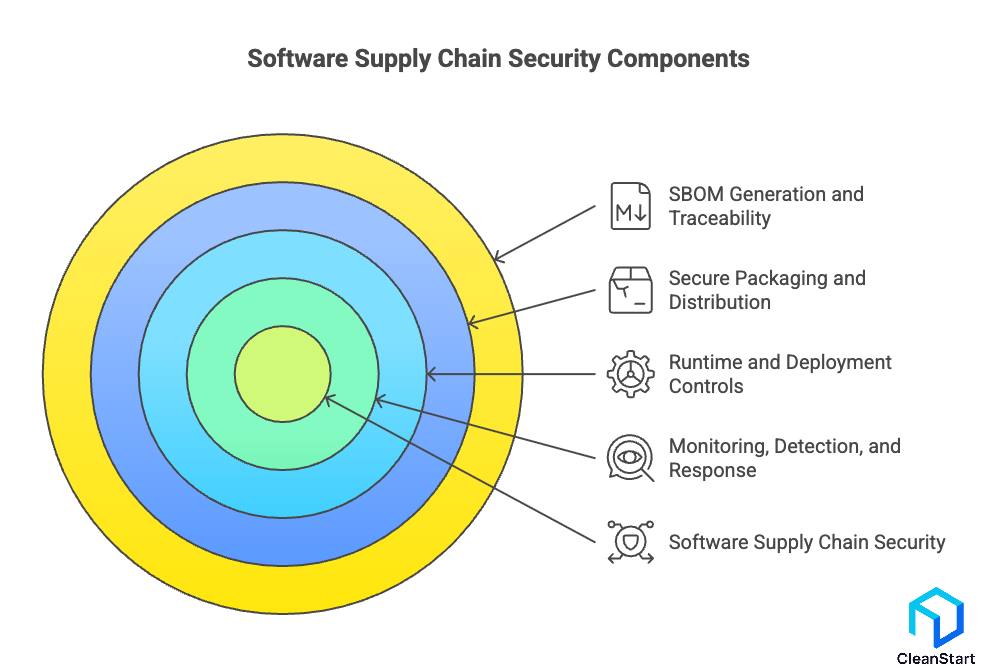
The following points are related to the key components of software supply chain security.
- Asset and dependency inventory
Maintain an accurate inventory of first-party code, third-party libraries, containers, base images, build tools, and services.
- Identity and access control
Enforce strong authentication and least privilege for developers, CI/CD systems, package publishing, repositories, and cloud accounts.
- Source integrity and change control
Protect source repos with branch protections, signed commits or tags where practical, required reviews, and tamper-evident audit trails.
- Build security and hardening
Use isolated and reproducible builds, hardened CI runners, pinned build inputs, secrets isolation, and controlled build permissions.
- Artifact integrity and provenance
Sign artifacts, generate provenance attestations, and verify signatures and attestations before promotion or deployment.
- Dependency and vulnerability management
Pin versions, use lockfiles, monitor for CVEs and malicious packages, and apply patching and rebuild cadences for images and dependencies.
- SBOM generation and traceability
Produce SBOMs for releases, store them with artifacts, and use them for impact analysis, audit evidence, and incident response.
- Secure packaging and distribution
Secure registries and package repos with access controls, immutability where appropriate, and scanning at publish and pull time.
- Runtime and deployment controls
Enforce policy at deploy time and runtime (admission controls, configuration baselines, network segmentation, and secrets management).
- Monitoring, detection, and response
Collect logs and telemetry across CI/CD, artifact stores, and production; alert on anomalous publishing, signing, and deployment events.
- Governance, standards, and compliance mapping
Map controls to frameworks such as SLSA, NIST SSDF, and secure development policies, and define evidence and ownership.
- Metrics and continuous improvement
Track measurable outcomes such as dependency freshness, mean time to patch critical CVEs, build policy compliance rate, and provenance coverage
What are the most common risks and threats in the software supply chain?
The following points are related to the most common risks and threats in a secure software supply chain.
- Compromised source control and developer identities: Attackers use stolen credentials (for example, a leaked GitHub personal access token with repository write access) to inject malicious code into part of the software before it is reviewed or released, undermining software security.
- Malicious or vulnerable third-party dependencies: Open-source packages and third-party libraries introduce supply chain from potential vulnerabilities, including typosquatting (for example, installing reqeusts instead of requests) and dependency confusion that pulls an attacker-controlled package.
- Transitive dependency exposure: Indirect dependencies expand the attack surface because a single top-level package can pull hundreds of nested libraries, increasing the chance of exploitable vulnerabilities and hidden malicious code in software components and dependencies, especially when a Dockerfile explicitly installs packages and pins base images to define what gets baked into the container build, causing those dependency choices to ship into production.
- CI/CD and build pipeline compromise: Build runners, build scripts, and pipeline plugins become a target because altering the build step can silently change the output artifact; this breaks the security of the entire software even when source code looks clean.
- Secrets leakage in pipelines and repositories: Exposed API keys, signing keys, or cloud credentials (for example, an .env file committed to a public repo) enable unauthorized access to build, release, and production systems, leading to security breaches.
- Artifact and repository tampering: Attackers replace or modify released binaries, container images, or packages in registries when access controls are weak, directly impacting software supply chain management and the security of your software supply.
- Weak provenance and integrity controls: If organizations cannot prove where an artifact came from, who built it, and which inputs were used, integrity of their software supply becomes unverifiable, making backdoors harder to detect.
- Insecure update and distribution channels: Compromised software update mechanisms allow attackers to push malicious updates at scale, turning a routine patch cycle into a supply chain incident.
- Vendor and service provider compromise: A breach at a build tool provider, dependency registry, or managed CI service can cascade into downstreamcustomers, making supply chain risk management a shared exposure across the integration of software supply chain ecosystems.
- Misconfigurations and policy gaps: Over-permissive roles, missing branch protections, and unsigned releases create avoidable openings; without enforceable security practices and a consistent security framework, teams cannot continuously integrate security across the pipeline.
What are software supply chain security best practices?
Software supply chain security best practices are the specific controls that keep a secure supply chain intact from source code to release artifacts and updates, so you can protect against software tampering and reduce the chance that part of the software supply is compromised.
The following points are related to best practices for software that secure the software supply chain and protect production releases.
- Lock down developer and CI identities: Require MFA for repository and CI access, use short-lived tokens for automation, and restrict write permissions to the smallest set of maintainers so one stolen credential cannot alter the supply chain.
- Enforce protected source control workflows: Require pull requests, mandatory reviews, signed commits where feasible, and branch protection rules so unreviewed code cannot reach main or release branches.
- Harden and isolate build systems: Run builds in ephemeral, least-privilege environments (for example, a fresh CI runner per pipeline job) to reduce persistence and limit lateral movement if a job is compromised.
- Verify dependencies before use: Pin versions, review new dependencies, and prefer vetted registries or curated mirrors to reduce software supply chain risk from malicious packages and reduce risk from typo-squatting, then lock down the container entrypoint command that launches the workload so only approved binaries and arguments run at startup, preventing untrusted tools from executing even if they slip into the image.
- Generate and store an SBOM per release: Produce an SBOM at build time and attach it to every release artifact so teams can trace what shipped when a new CVE hits a dependency.
- Sign artifacts and verify signatures at deployment: Sign container images, packages, or binaries and reject unsigned artifacts in deployment pipelines to prevent artifact substitution in registries.
- Add policy gates with automated checks: Use automation of security in CI to block releases on high-severity vulnerabilities, exposed secrets, or policy violations, so integration of security happens before production.
- Secure secrets end to end: Store secrets in a dedicated secret manager, rotate credentials, and prevent secrets from entering repos or logs to reduce common compromise paths.
- Monitor build and release activity: Alert on unusual publish events (for example, a new package version released from an unfamiliar CI identity) to catch early signs of a supply chain incident.
- Practice recovery and supplier risk controls: Maintain rollback-ready release processes, document supplier dependencies, and run periodic access and configuration reviews so you improve the security posture of the entire pipeline over time.
What is a software supply chain attack?
A software supply chain attack is a compromise where an attacker targets the systems and relationships used to build, distribute, or update software, so malicious code reaches users through a trusted channel instead of through a direct attack on the running application. For example, the SolarWinds Orion incident (publicly disclosed in December 2020) involved tampering in the build and release process so customers received a backdoored update that appeared legitimate.
What are examples of software supply chain attacks?
The following points are related to examples of software supply chain attacks, ordered from most recent to older:
- Widespread npm ecosystem compromise (September–November 2025)
Multiple widely used npm packages were compromised and malicious versions were published, impacting downstream builds through normal dependency installs.
(Ref: CISA.gov)
- XZ Utils backdoor attempt (March 2024, CVE-2024-3094)
Malicious code was introduced into upstream xz/liblzma releases, creating downstream risk via Linux distributions and packages.
(Ref: RedHat.com, NVD.NIST.gov).
- 3CX DesktopApp (March 2023)
A trojanized, signed desktop app installer/update path was used to deliver a staged compromise to downstream users. (Ref: CISA.gov, CrowdStrike.com)
- Codecov Bash Uploader compromise (2021)
A modified uploader script was used to exfiltrate secrets from CI environments running it. (Ref: Codecov.io )
- Kaseya VSA (July 2021)
An RMM platform was abused to push ransomware to many downstream endpoints, scaling impact through MSP tooling. (Ref: CISA.gov).
- SolarWinds Orion (2020)
Malicious code was inserted into a trusted vendor update channel, enabling compromise downstream after customers installed the update.
(Ref: CISA.gov, Microsoft Security Blog)
- npm event-stream (2018)
A popular open-source dependency was modified so downstream projects pulled malicious code during routine installs. (Ref: Snyk.io )
- NotPetya via M.E.Doc updates (June 2017)
A software vendor’s update mechanism was used to distribute destructive malware at scale. (Ref: NCSC.gov.uk and government/industry incident reports.
- CCleaner (2017)
A compromised version was distributed via official channels, abusing user trust in a widely downloaded utility. (Ref: Cisco Talos Blog, Avast Blog)
What is the importance of software supply chain security?
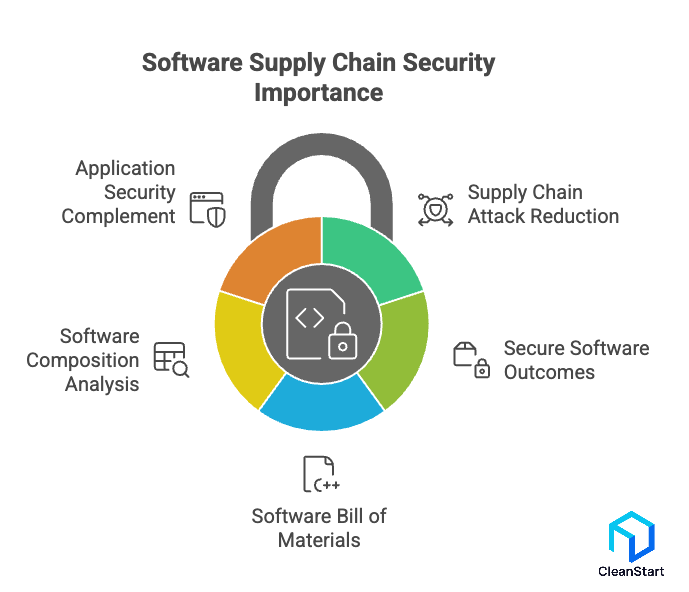
The following points are related to what software supply chain security covers in real software development and why it matters.
- It reduces supply chain attacks by verifying what goes into modern software, including open source software packages, third-party libraries, and build outputs.
- It strengthens secure software outcomes by tracking software composition and applying container security controls that scan and enforce policies on container images to catch vulnerable packages and misconfigurations, continuously checking for security issues introduced by dependencies, build pipelines, or compromised accounts.
- It uses a software bill of materials to document the exact dependency set and versions used in a release (for example, a CycloneDX or SPDX SBOM generated at build time and stored alongside the release artifact).
- It relies on software composition analysis to detect vulnerable or malicious dependencies before they reach production, improving how security teams measure and improve overall security posture.
- It complements application security by covering risks outside the app’s own code, such as dependency provenance, build integrity, and artifact integrity, so you can secure the software supply chain end to end using enforceable best practices.
Which stages make up the end to end software supply chain?
The end-to-end software supply chain is the full sequence of activities and systems involved in the creation and deployment of software, starting when software is developed and ending when a software update is delivered and running in production. A modern software supply chain typically includes these stages, with security checks and security measures applied throughout the software development lifecycle to reduce supply chain security risks and prevent a software supply chain attack, including runtime controls like cgroups that limit a container’s CPU and memory usage to contain resource abuse and reduce blast radius if compromised code reaches production.
The following points are related to the stages that make up the entire software supply chain.
- Plan and design: Define requirements, architecture, security policies, and compliance with security expectations early in the software development process to reduce potential security risks before code is written.
- Source code development: Build the piece of software using development tools, enforce secure software development practices, and integrate security into daily workflows to prevent security flaws from entering the codebase.
- Third-party intake and dependency management: Select and control third-party software dependencies, including open-source software components, to reduce vulnerabilities in the software supply and limit supply chain threats from untrusted packages.
- Build and package: Compile and package outputs into a software artifact (for example, a signed container image or release binary), automate security and integrity controls, and enforce security policies so tampering becomes detectable.
- Security testing and verification: Run security testing such as static application security testing and dynamic application security testing, plus policy-based security checks and software supply chain security tool scans, to identify software vulnerabilities before release.
- Release and distribution: Publish artifacts to registries or repositories, enforce access controls and signing verification, and apply robust security measures to reduce the chance of security breaches during distribution.
- Deployment of software: Deploy to environments where software systems run, apply supply chain security in DevSecOps with gated promotions and enforced security policies, and validate that only approved artifacts reach production.
- Runtime operations and monitoring: Monitor for emerging supply chain threats, drift, and compromise signals, and use proactive approach to security to detect and respond to risks in the software supply after deployment.
- Software update and patching: Ship software update releases safely by repeating the same end-to-end software supply chain security controls, ensuring the security of software supply chains remains consistent across versions
Which standards and frameworks apply to software supply chain security?
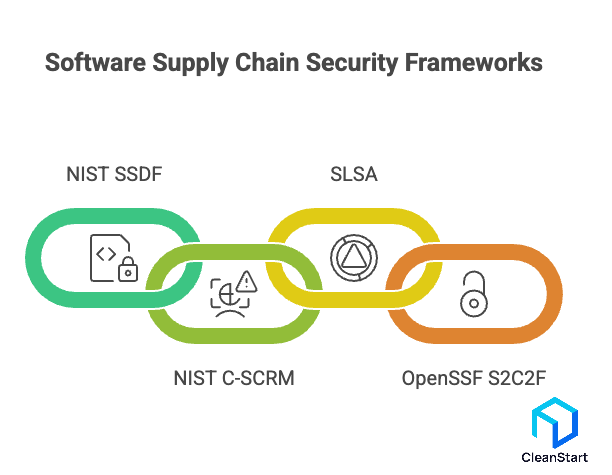
Several widely used standards and frameworks apply to software supply chain security, covering secure development, supply chain risk management, build integrity, and open-source dependency consumption, including controls that extend into container orchestration platforms that schedule and run containers at scale, where admission policies and image verification can enforce that only trusted artifacts are deployed.
The following points are related to standards and frameworks that organizations use to secure software supply chains and protect downstream users.
- NIST Secure Software Development Framework (SSDF), SP 800-218: A secure software development baseline that maps practices and tasks across the SDLC (for example, integrating threat modeling, secure coding, testing, and release integrity controls into a CI pipeline used for every production build).
- NIST Cybersecurity Supply Chain Risk Management (C-SCRM), SP 800-161 Revision 1: A supply-chain risk management framework for identifying, assessing, and mitigating cybersecurity risks across suppliers, services, and dependencies (for example, defining supplier requirements for artifact signing and SBOM delivery in procurement contracts).
- SLSA, Supply-chain Levels for Software Artifacts: A maturity model for build integrity and provenance that helps teams increase assurance from source to service (for example, using authenticated builds and provenance attestation for a container image released from a GitHub Actions pipeline).
- OpenSSF Secure Supply Chain Consumption Framework, S2C2F: A consumption-focused framework for securely ingesting open-source dependencies into developer workflows (for example, requiring approved package sources and verification steps before a dependency can be used in production builds).
How do you choose software supply chain security tools and platforms?
Choose software supply chain security tools and platforms by matching capabilities to the control points you actually operate across the SDLC (source, dependencies, build, artifact, deploy, update), then validating they produce enforceable outcomes in your pipelines.
The following points are related to selecting software supply chain security tools and platforms that secure the chain and protect your organization.
- Start from your pipeline reality, not the vendor checklist: Map your current toolchain (for example, GitHub, GitLab, Jenkins, Artifactory, Nexus, container registries, Kubernetes) and include the container runtime layer such as containerd or CRI-O that actually pulls and executes images on nodes, then require native integrations or stable APIs for every critical hop.
- Prioritize prevention controls over “reporting-only” features: Prefer tools that can block a release when policy fails (for example, fail the build if a dependency has a known exploitable vulnerability with CVSS ≥ 7.0 and no fix available, or reject a container image at admission if it is unsigned).
- Require end-to-end artifact integrity: Look for artifact signing, verification, and tamper resistance across registries and deployment of software (for example, signing OCI images at build time and verifying signatures in Kubernetes admission before rollout).
- Demand high-fidelity dependency coverage: Ensure strong software composition analysis for direct and transitive dependencies, including open-source ecosystems you actually use (for example, npm, PyPI, Maven, Go modules), with clear remediation guidance tied to exact package versions.
- Make SBOM and provenance first-class outputs: Pick platforms that generate and store SBOMs and provenance per build (for example, producing SPDX or CycloneDX SBOMs and attaching them to the release artifact so you can trace exposure when a new CVE drops).
- Enforce policy centrally, execute locally: Prefer a model where security policies are defined once (for example, “no critical vulns in production releases” and “only approved registries allowed”) and enforced consistently across CI, artifact repositories, and deploy gates.
- Cover the highest-risk breach paths: Ensure the platform addresses secrets leakage, CI/CD compromise, and artifact substitution (for example, secret scanning on pull requests, hardened build runner recommendations, and registry immutability controls).
- Check signal quality and operational cost: Validate false positive rates and workflow noise by running it on one real service for two weeks and measuring the number of blocked builds, true positives, and time-to-fix for top findings.
- Validate enterprise constraints early: Confirm data residency, RBAC, audit logs, and exportability (for example, “can we export findings, SBOMs, and provenance as JSON and retain them for 12 months for audits”).
- Pilot against a concrete use case: Use one representative “examples of software supply chain” workload (for example, a Node.js API with 200+ dependencies and a containerized deploy) and require measurable outcomes before purchase (blocked high-risk releases, signed artifacts enforced, SBOM produced per build, and verified deploy gates).
What metrics should you track to measure software supply chain security?
To measure software supply chain security, track metrics that quantify integrity, dependency risk, build and release assurance, and how fast you can remediate when new issues appear.
The following points are related to measurable indicators of software supply chain security across the software development lifecycle.
- SBOM coverage rate: Percentage of production releases that publish a Software Bill of Materials (for example, 92 of 100 releases in Q4 2025 include an SPDX or CycloneDX SBOM stored with the release artifact).
- Provenance attestation coverage: Percentage of production builds that generate verifiable build provenance (for example, 80% of container images pushed to the registry have provenance linked to the exact commit and CI workflow run).
- Artifact signing and verification rate: Percentage of released artifacts that are signed and rejected if unsigned at deploy time (for example, 100% of Kubernetes deployments enforce signature verification at admission).
- Policy gate effectiveness: Number and percentage of builds blocked by enforced rules (for example, 14% of release candidates blocked because a critical vulnerability was present or a policy requirement failed).
- Mean time to remediate vulnerable dependencies: Median days from vulnerability disclosure to fix deployed for dependencies (for example, median 9 days for high severity issues in third-party libraries across production services).
- Exposure window for known vulnerabilities: Total time a known vulnerable component exists in production (for example, Log4j-like dependency exposure measured from detection to removal across all affected services).
- Critical vulnerability density in dependencies: Critical or high vulnerabilities per application based on software composition analysis results (for example, 0.6 critical vulnerabilities per service per monthly scan).
- Transitive dependency growth rate: Change in indirect dependency count per release (for example, a Node.js service increases from 420 to 510 transitive packages over 6 releases, increasing audit scope).
- Secrets exposure rate: Count of verified secrets found in repos, CI logs, or artifacts per month (for example, 3 confirmed credential leaks in Git history in November 2025).
- Privileged pipeline access footprint: Number of identities with release-publish permission and how often they are used (for example, only 4 CI service accounts can publish artifacts; all publish actions are logged).
- Unauthorized or anomalous release attempts: Count of blocked publish events from unexpected identities, locations, or workflows (for example, a package publish blocked because it came from a non-approved CI runner).
- Rollback and recovery readiness: Mean time to rollback a bad release and percentage of services with a tested rollback procedure (for example, 95% of production services can roll back within 15 minutes).
- Supplier risk completion rate: Percentage of critical third-party software suppliers with documented security requirements and review status (for example, top 20 vendors reviewed annually with evidence retained for audits).
What are the latest trends and emerging technologies in software supply chain security?
The following points are related to the latest trends and emerging technologies shaping software supply chain security.
- SBOM becomes a regulatory and audit artifact, not a “nice to have”: EU Cyber Resilience Act guidance and industry commentary increasingly treat SBOM creation and retention as a lifecycle obligation for products with digital elements (for example, maintaining an SBOM for each released version through 2026 enforcement timelines).
- SBOM becomes actionable through VEX and structured advisories: Teams are pairing SBOM inventories with VEX-style exploitability statements so a CVE in a dependency is classified as exploitable or not exploitable in a specific runtime context (for example, “present but not reachable in production”).
- Provenance-first security using SLSA levels and attestations: Adoption is shifting from “scan what you built” to “prove how you built it,” with signed, tamper-resistant provenance and isolated builds becoming common target states (for example, SLSA-aligned provenance attached to every container image produced by a CI workflow).
- Keyless signing and transparency logs move into mainstream pipelines: Sigstore-style signing lowers operational friction by using short-lived certificates and transparency logs, making artifact verification practical at scale (for example, signing OCI images at build time and verifying before Kubernetes rollout).
- End-to-end supply chain verification with in-toto: in-toto attestations are being used to make build steps verifiable and ordered, and its CNCF graduation signals maturity and broader enterprise adoption (for example, verifying “tests ran” and “release was signed” before promotion).
- Secure software update frameworks gain renewed focus: TUF and TUF-as-a-service patterns are being adopted to harden update channels against repository compromise and key compromise (for example, resilient metadata-driven update verification for client updaters).
- Confidential computing and remote attestation enter build trust discussions: Remote attestation is increasingly used to prove a build ran in an expected environment before trusting the resulting artifact (for example, attesting a hardened build runner configuration before issuing signing keys).
- AI changes both the attack surface and the defense surface: AI-assisted coding increases dependency and code ingestion risk, while organizations respond by adding stricter verification for generated code and licensing, plus automated scanning tuned for supply chain issues (for example, treating AI-generated pull requests as higher-risk changes that must pass stronger gates).
- Identity-aware supply chain controls: Workload identity systems increasingly use “built and signed by trusted CI” as an access condition (for example, only allowing deployment credentials when the artifact is signed and provenance matches an approved pipeline).
What is the difference between software supply chain security and application security?
What is an SBOM and how does it improve software supply chain security?
An SBOM (Software Bill of Materials) is a machine-readable inventory of the software components used to build a product, including component identities, versions, and supply-chain relationships (for example, which library was pulled in by another dependency).
The following points are related to how an SBOM improves software supply chain security for real software applications.
- Faster vulnerability response: When a CVE is disclosed, an SBOM lets security teams answer “Are we affected?” by matching the vulnerable package name and version to shipped releases (for example, checking whether any production image built on 2025-12-01 includes log4j-core 2.14.1).
- Better dependency transparency: SBOM formats like CycloneDX can represent complete inventories and relationships, making transitive dependency exposure visible instead of hidden inside build logs.
- Stronger governance and procurement controls: SBOM “minimum elements” guidance helps standardize what suppliers provide, so component transparency can be contractually required and audited across your supply chain using consistent fields.
- More reliable incident scoping: During a supply chain incident, an SBOM narrows investigation to the exact releases and artifacts that included a compromised component, reducing guesswork and improving containment decisions.
FAQs
- How do we assign ownership for software supply chain security without slowing delivery?
Assign one accountable owner for policy and guardrails (usually Platform Engineering or AppSec), then keep remediation ownership with the service teams. Treat it like reliability: centralized standards, distributed execution.
- What “evidence pack” should we request from software vendors and open-source suppliers?
Ask for an SBOM per released version, a clear security advisory process, patch timelines for critical CVEs, and proof of release integrity (signing and verifiable build provenance). This turns supplier risk into verifiable controls, not promises.
- How often should we rebuild container images even when application code has not changed?
Rebuild on a fixed cadence (for example weekly) and immediately when a base-image or critical dependency CVE lands. The goal is to shrink the vulnerability exposure window, not just “patch when convenient.”
- How do we enforce “only trusted artifacts deploy” in Kubernetes without breaking developer flow?
Use admission controls to verify signatures and provenance at deploy time, but keep it fast by validating promoted, immutable artifacts (same digest across environments) and caching verification results. Developers keep shipping; the cluster blocks only untrusted artifacts.
- What should incident response look like for a suspected supply chain compromise?
Freeze releases, isolate affected build systems, rotate signing and CI credentials, and identify the first bad artifact by comparing digests, provenance, and release logs. Then revoke and replace compromised artifacts, and communicate impact based on exact affected versions (SBOM-backed scoping).



