CIS Benchmarks for Docker and Kubernetes Hardening
Misconfigurations are where container breaches usually start. This guide explains what CIS Benchmarks are, what the CIS Docker Benchmark and CIS Kubernetes Benchmark cover, how they strengthen hardening, how to run and assess compliance with common tools, how Level One and Level Two differ, how benchmarks support compliance, and what challenges teams face.
What are CIS Benchmarks for Docker and Kubernetes hardening?
CIS Benchmarks for Docker and Kubernetes hardening are prescriptive, consensus-developed secure configuration guidelines published by the Center for Internet Security to reduce configuration-driven cybersecurity risk and exposure to cyber threats.
For Docker, the CIS Docker Benchmark defines secure configuration recommendations across the Docker ecosystem (for example, host settings, Docker daemon configuration, container runtime settings, and image build practices) so teams can harden Docker deployments using a consistent configuration baseline.
For Kubernetes, the CIS Kubernetes Benchmark defines secure configuration recommendations for Kubernetes clusters (for example, control plane and node settings) so teams can harden cluster configuration and reduce attack paths that originate from weak defaults or misconfiguration.
What is the CIS Kubernetes Benchmark?
The CIS Kubernetes Benchmark is a consensus-based secure configuration standard for hardening Kubernetes clusters. It defines prescriptive configuration checks that security teams use as a best practice baseline to reduce misconfiguration risk.
If you need to automate assessment, CIS provides tooling such as CIS-CAT Pro, which is available to CIS SecureSuite members and is designed to automate CIS Benchmark assessment and reporting.
What is the CIS Docker Benchmark?
The CIS Docker Benchmark is a secure configuration standard from the Center for Internet Security that provides security recommendations to harden the Docker container ecosystem and reduce attack surface caused by insecure defaults and misconfigurations.
How do CIS Benchmarks help with Docker and Kubernetes hardening?
CIS Benchmarks help with Docker and Kubernetes hardening by providing clear, testable security configuration standards that reduce real-world risk from misconfigurations, insecure defaults, and operational drift across containerized environments.
For Docker, CIS Benchmarks improve security hardening by:
- Defining strict rules for file permissions, file ownership, and sensitive directory access in Docker configuration files, which reduces host-level compromise.
- Enforcing secure dockerfile practices and controls for container images, lowering vulnerability introduction during build and deployment.
- Recommending Docker Content Trust (DCT) to validate image provenance and prevent the use of untrusted or tampered images.
- Providing remediation guidance to validate findings, safeguard secrets such as tokens and passwords, and reduce overall attack surface.
For Kubernetes, the Kubernetes CIS Benchmark strengthens secure Kubernetes deployments by:
- Hardening the API server, controller, kubelet, and worker nodes to prevent unauthorized access and privilege escalation.
- Enforcing strong authentication, namespace isolation, and secure security configuration for cluster components.
- Reducing risk of cluster-wide compromise caused by weak defaults in control plane and node settings.
- Enabling automated assessment with tools like kube-bench to scan your systems and continuously validate compliance against documented CIS controls, while your container registry image store enforces approved image sources and tag immutability so only compliant builds are available for deployment.
Across both platforms, CIS Benchmarks:
- Provide security standards that DevOps teams can apply consistently in real-world environments.
- Support compliance frameworks such as SOC, PCI DSS, and HIPAA by offering auditable configuration baselines.
- Maintain versioned guidance, with a list of archived CIS benchmarks available for reference when benchmarks are no longer supported by CIS, while encouraging teams to download the latest active versions.
- Benefit from the CIS Benchmarks Community, ensuring guidance remains practical, vendor-neutral, and based on operational experience.
How do you run CIS Benchmarks for Docker and Kubernetes?
You run CIS Benchmarks for Docker and Kubernetes by assessing your environment against the official CIS configuration checks and validating whether your systems align with the recommended security baselines, so your container security posture reflects secure configuration across images, runtimes, and cluster components rather than relying on assumptions.
For Docker, the process typically involves:
- Using assessment tools that are based on the CIS Docker Benchmark to evaluate daemon settings, host configuration, and container runtime behavior.
- Verifying whether hardened images and Docker build practices align with CIS requirements.
- Comparing findings against the official CIS Benchmark documentation, which is also available as a PDF for reference and manual validation.
For Kubernetes, the process generally includes:
- Running automated tools that check cluster components against controls documented in the CIS Kubernetes Benchmark.
- Evaluating control plane components, node configuration, and workload settings against CIS recommendations, while using an SBOM to inventory every packaged dependency in each container image so you can trace what is deployed when a new vulnerability is disclosed.
- Ensuring results are mapped to the correct benchmark version, especially when dealing with clusters created using older Kubernetes releases.
Across both platforms:
- CIS Benchmarks are executed by validating live system configuration rather than scanning application code.
- Results indicate pass, fail, or manual review items, allowing teams to prioritize remediation.
- Older checks from benchmarks that are no longer active remain available for historical reference, but assessments should always target the current benchmark version where possible.
- The goal is to consistently measure real system state against CIS-defined expectations, not theoretical configuration.
Which tools are used to assess CIS Benchmark compliance?
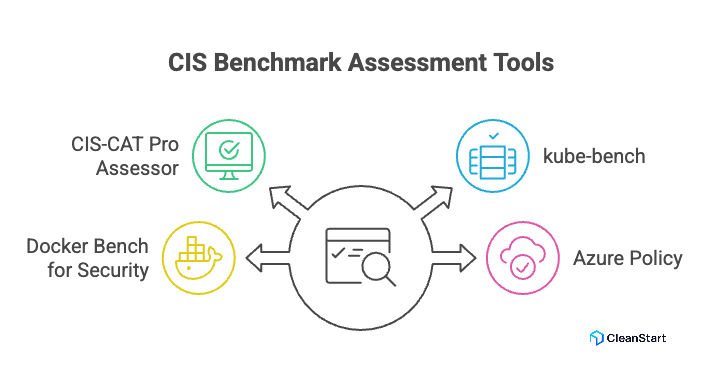
Tools commonly used to assess CIS Benchmark compliance for Docker and Kubernetes include:
- CIS-CAT Pro Assessor to automate assessment and reporting against CIS Benchmarks (available via CIS SecureSuite).
- kube-bench to assess Kubernetes clusters by running checks documented in the CIS Kubernetes Benchmark.
- Docker Bench for Security to assess Docker hosts and containers using tests that are based on the CIS Docker Benchmark.
- For Azure managed Kubernetes, AKS commonly uses Azure Policy built-in policy definitions that map to specific CIS Kubernetes Benchmark recommendations at the pod and cluster level.
What are common CIS Benchmark challenges for Docker and Kubernetes?
Common challenges with CIS and the CIS Benchmarks for Docker and Kubernetes come from the gap between prescriptive secure configuration and real production constraints:
- Production compatibility risk: Some CIS settings can break workloads, networking, or storage assumptions when applied without workload-specific testing.
- Shared responsibility ambiguity: Teams often misassign ownership between platform, DevOps, and security, so findings remain open without remediation, especially when cgroups resource controls that enforce CPU and memory limits are treated as “someone else’s layer” and never consistently configured or validated.
- Kubernetes control plane constraints: Managed Kubernetes limits control plane changes, so some CIS checks cannot be implemented directly by the customer.
- Benchmark version drift: Clusters and Docker hosts change faster than benchmark rollouts, creating mismatches between the evaluated version and the deployed version.
- False positives and context gaps: Automated checks can flag secure intentional exceptions as failures when the tool lacks environment context.
- Exception handling weakness: Organizations allow exceptions without consistent documentation, expiration, or compensating controls, reducing audit value.
- Operational overhead: Continuous scanning, reporting, and remediation tracking adds recurring workload, especially across many clusters and environments.
- Inconsistent baseline enforcement: Different teams apply different interpretations of “secure configuration,” so the environment becomes non-standard and harder to validate.
- Hardening versus usability trade-offs: Stronger restrictions can increase friction for developers and operators, causing bypass behaviors or rollback pressure.
What is the difference between CIS Level One and Level Two benchmarks?
CIS Benchmarks typically include two configuration profiles, Level 1 and Level 2, that differ by security strictness and operational impact.
- CIS Level 1 is the baseline profile. It focuses on essential, broadly applicable hardening recommendations that are intended to be implemented relatively quickly and to have minimal impact on system performance or usability.
- CIS Level 2 is the defense-in-depth profile. It adds stricter recommendations for higher-risk or higher-sensitivity environments, and it can reduce functionality or increase operational complexity if applied without careful testing and change control, especially when hardening requires locking down the container entrypoint startup command that controls which process runs first and which privileges and file paths it can access.
How do CIS Benchmarks support compliance and regulatory requirements?
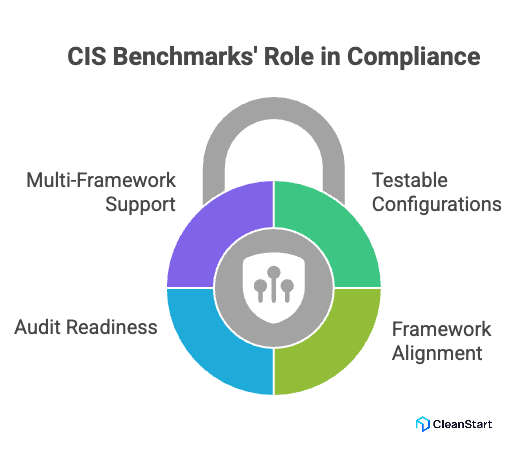
CIS Benchmarks support compliance and regulatory requirements by giving organizations a prescriptive, auditable secure configuration baseline that can be used as evidence during internal control reviews and external audits. CIS positions the CIS Controls and CIS Benchmarks as resources that help organizations “show compliance” while defending against emerging threats.
- They translate high-level requirements into testable configurations. CIS Benchmarks define secure configuration recommendations for specific technologies, which makes compliance work measurable as pass fail configuration outcomes instead of policy statements.
- They align with broader compliance frameworks through mappings. Microsoft’s compliance documentation notes that CIS recommendations map to CIS Controls, and CIS Controls map to widely used frameworks including NIST CSF, NIST SP 800-53, ISO 27000 series, PCI DSS, and HIPAA.
- They strengthen audit readiness with standardized baselines. Using a consistent benchmark baseline across environments helps produce repeatable evidence for audit sampling, exception tracking, and remediation verification, especially when container orchestration platforms like Kubernetes enforce the same workload policies and configuration settings across clusters and namespaces.
- They support multi-framework compliance programs. CIS explicitly maintains mappings resources so teams can streamline conformance across multiple frameworks rather than building separate control interpretations for each standard.
FAQs
- What versions of Kubernetes and Docker do CIS Benchmarks apply to?
CIS Benchmarks are version-specific and must match the exact Docker or Kubernetes version in use to produce accurate results.
- Can CIS Benchmarks be applied to managed Kubernetes services?
Yes, but some controls may be non-configurable due to provider-managed control planes, requiring documented exceptions.
- Do CIS Benchmarks replace vulnerability scanning tools?
No. CIS Benchmarks focus on secure configuration, while vulnerability scanners identify known software flaws. Both are complementary.
- How often should CIS Benchmark assessments be run?
They should be run continuously or after configuration changes, cluster upgrades, or new workload deployments.
- Are CIS Benchmarks suitable for production environments?
Yes, but controls should be applied incrementally with testing, especially for Level Two recommendations.
- Do CIS Benchmarks guarantee security?
No. They reduce risk from misconfiguration but do not eliminate threats such as zero-day exploits or supply-chain attacks.



