SOC 2 Compliance for Container Based SaaS Applications
If your SaaS runs on containers, proving trust is not optional. This article explains what SOC 2 means for SaaS, the core requirements, who needs it, how SOC 2 reporting works, and how to implement controls in container and cloud environments—plus ongoing compliance, common mistakes, consequences, and FAQs.
What is SOC 2 for SaaS?
SOC 2 for SaaS is an AICPA-defined assurance framework where an independent auditor (typically a CPA firm) performs a SOC 2 audit and issues a SOC 2 report that evaluates whether a SaaS provider’s security controls meet the Trust Services Criteria for protecting customer data (including personal data and other sensitive data) in its cloud infrastructure.
For SaaS companies, SOC 2 is used to demonstrate security and compliance readiness through documented compliance requirements, defined control objectives, and evidence collection, including container image provenance and scan evidence that shows what code and dependencies are shipped, alongside log records of security events and access activity, which an auditor tests against the applicable criteria.
When do SaaS companies need a SOC 2?
SaaS companies need SOC 2 when customers, regulators, or enterprise procurement teams require independent assurance that the platform securely handles customer environments, operational processes, and data lifecycle controls. SOC 2 is typically adopted at the point where trust, risk visibility, and vendor due diligence become revenue-critical.
- When selling to enterprise or regulated buyers who request third-party assurance of security and operational controls.
- When the product stores or processes customer systems, configurations, or operational data in a shared cloud environment.
- When vendor risk assessments require documented control validation before contract approval.
- When scaling from early-stage product to enterprise-ready platform and trust becomes a buying factor.
- When competitive deals are lost to vendors that already have independent assurance.
- When internal governance maturity requires structured control validation and accountability.
- When leadership wants a formal trust signal—SOC 2 offers externally validated assurance rather than internal-only security claims.
What are common SaaS applications that need SOC 2 compliance?
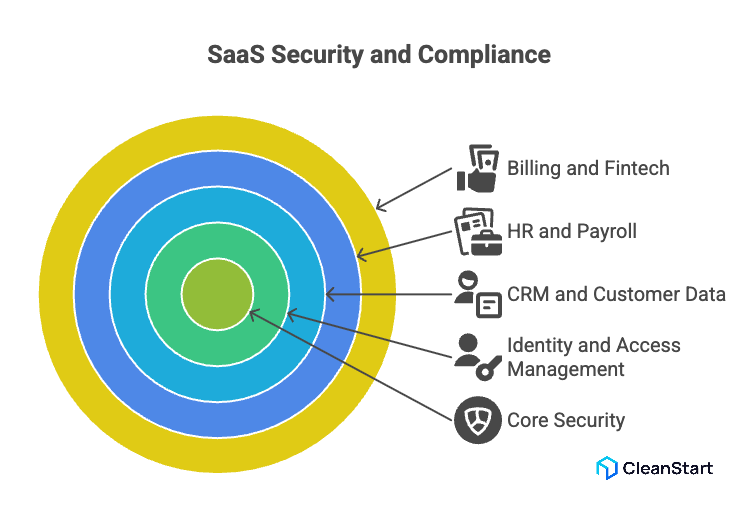
Common SaaS applications that need SOC 2 compliance are cloud services that store, process, transmit, or administer personal information, sensitive customer records, or other customer data, where buyers expect tested access control, authentication, encryption, incident handling, and disaster recovery planning aligned to the AICPA Trust Services Criteria (including confidentiality and processing integrity) and evidenced through compliance reports such as a Type II / type 2 report, supported by container security controls that harden runtime isolation and continuously detect misconfigurations or vulnerable images that could expose customer data.
- Identity and access management SaaS (access management, authentication)
- CRM and customer data SaaS (personal information, confidentiality)
- HR and payroll SaaS (personal information, access control)
- Billing and fintech SaaS (processing integrity, risk management)
- Healthcare SaaS (HIPAA-aligned security posture)
- Data and analytics SaaS (cloud security, encryption)
- DevOps and CI/CD SaaS (security controls, maintaining compliance)
- Monitoring, logging, and security SaaS (security events, breach readiness)
- Backup and disaster recovery SaaS (disaster recovery planning)
- Support and ticketing SaaS (confidentiality, access control)
- Marketing automation SaaS (personal information, GDPR)
- Integration and iPaaS SaaS (third-party data movement, access control)
What are SOC 2 compliance requirements for SaaS companies?
SOC 2 compliance requirements for SaaS companies are defined by the American Institute of Certified Public Accountants (AICPA) under the SOC reporting standard. To achieve SOC 2 compliance, a SaaS provider must design, implement, and demonstrate operational controls that align with the five Trust Services Criteria (Security, Availability, Processing Integrity, Confidentiality, Privacy), with Security (the common criteria) forming the mandatory baseline for every engagement. In container-based SaaS, containerization standardizes how application services are packaged and deployed, so auditors can trace which workloads run where and verify that controls operate consistently across environments. According to the Institute of Certified Public Accountants, SOC 2 evaluates whether controls are suitably designed and operating effectively at a specific point in time or over a defined review period.
Core SOC 2 compliance requirements for SaaS companies include:
- Establishing governance aligned with recognized compliance frameworks and demonstrating a documented commitment to security.
- Implementing controls that prevent unauthorized access, reduce vulnerability exposure, and protect customer environments.
- Performing a formal readiness assessment to identify control gaps before the audit.
- Designing policies and operational processes to achieve compliance and sustain them over time.
- Demonstrating control effectiveness through evidence and auditor validation at a defined point in time or across an operating period.
- Aligning security practices with regulatory expectations where applicable (for example, mapping to sector requirements such as HIPAA).
- Applying automation where possible to automate monitoring, control enforcement, and evidence generation as a best practice for maintaining control maturity.
These requirements collectively enable SaaS organizations to achieve SOC 2 compliance and maintain a verifiable security posture under the AICPA SOC assurance model, where cgroups enforce per-container CPU and memory limits that reduce noisy-neighbor risk and support availability-focused control outcomes.
What are SaaS compliance options if SOC 2 is not the only path?
SaaS compliance options when SOC 2 is not required depend on your customer segment, regulated data types (especially personally identifiable information and sensitive customer data), and your contractual compliance demands, including how your Dockerfile defines the build steps and base images that determine what software is packaged and what vulnerabilities may be introduced. Common alternatives include:
- ISO/IEC 27001 certification (ISMS) for organization-wide security governance, risk-based controls, and ongoing compliance management.
- PCI DSS if your SaaS stores, processes, or transmits payment card data, to reduce compliance risks tied to cardholder data and cloud security failures.
- HIPAA Security Rule alignment if you handle regulated ePHI as a covered entity or business associate, with required safeguards for confidentiality, integrity, and security.
- GDPR compliance if you process EU/EEA personal information, focusing on lawful processing and protection obligations for personal data.
- FedRAMP authorization if you sell a cloud service to U.S. federal agencies, using a standardized approach to assessment, authorization, and continuous monitoring.
- CSA STAR participation/certification to demonstrate cloud security assurance and transparency about the standards and frameworks you adhere to.
- SOC 3 if you want a public, general-use assurance report related to the Trust Services Criteria, but with less detail than a SOC 2 report.
How Do You Implement SOC 2 Controls for Container Based SaaS Applications?
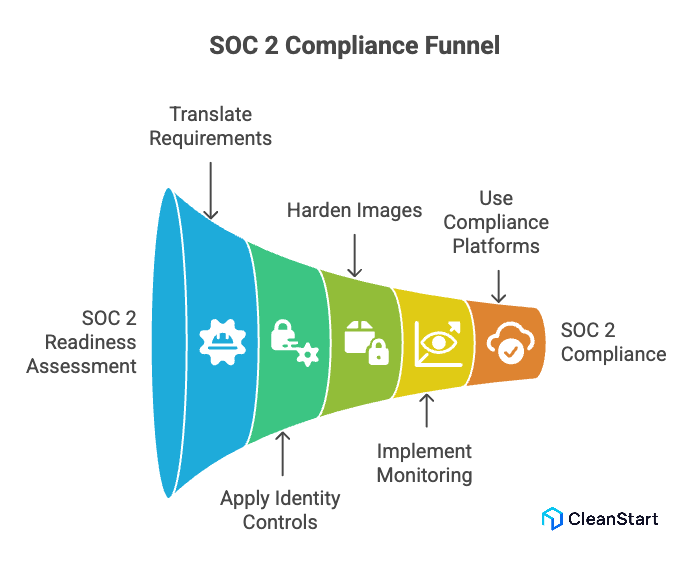
Implementing SOC 2 controls for container-based SaaS applications requires aligning cloud-native engineering practices with the SOC 2 requirements defined under the SOC 2 Trust Services criteria and embedding them into the software delivery lifecycle for continuous compliance.
- Begin with a SOC 2 readiness assessment to identify compliance gaps in container orchestration, identity design, logging, and operational controls based on the services the platform delivers.
- Translate the specific SOC 2 compliance requirements into technical safeguards for Kubernetes, container registries, CI/CD pipelines, and runtime environments.
- Apply identity-centric controls that help comply with SOC 2, including workload identity, role-based access, and secure secrets handling across environments.
- Harden container images and supply chains to meet SOC 2 expectations for integrity, traceability, and controlled deployment.
- Implement monitoring, alerting, and incident workflows that support continuous compliance across ephemeral infrastructure.
- Use compliance automation platforms or a centralized compliance platform to map controls, track evidence, and operationalize a SOC 2 compliance checklist across engineering and security teams.
- Embed governance into the CI/CD lifecycle so that SOC 2 compliance involves policy enforcement, automated checks, and approval gates at build and deploy stages.
- Maintain documentation and evidence that supports a future SOC 2 Type II or type 2 audit, demonstrating control operation over time.
- Regularly reassess architecture and workflows to close emerging potential compliance risks and sustain the SOC 2 journey from readiness to continuous compliance.
How do you establish a tailored compliance framework for SaaS?
Establishing a tailored compliance framework for SaaS means aligning security, privacy, and operational controls to the product’s data flows, customer expectations, and regulatory exposure rather than applying a generic model. For B2B SaaS, the framework must reflect contractual obligations, industry standards, and the risk profile of the platform, including how the container entrypoint starts the service process and enforces runtime defaults that affect logging, privilege level, and safe execution.
- Define scope first: map data types, tenants, infrastructure layers, and vendor dependencies to identify different compliance needs across products and regions.
- Use a baseline model such as understanding SOC 2 compliance as a reference point, then adapt controls to architecture, tenancy model, and delivery model.
- Identify which controls are required for SOC 2 versus those adopted as voluntary compliance to strengthen trust, sales readiness, and enterprise procurement alignment.
- Document control objectives and policies that demonstrate a commitment to security, privacy, and operational accountability.
- Evaluate the differences between SOC 2 control expectations and other frameworks to avoid duplication and reduce operational overhead.
- Build a practical operating model using a guide to SOC 2 compliance as structure, but tailor monitoring, logging, and governance to the SaaS lifecycle.
- Align internal processes so every SOC 2-aligned control supports real engineering workflows rather than audit-only activities.
- Treat compliance as a product capability: think of SOC 2 as a trust framework that supports customer assurance, vendor reviews, and enterprise sales readiness rather than a one-time certification.
What are common SOC 2 mistakes SaaS companies make during implementation?
Common SOC 2 mistakes SaaS companies make during implementation usually stem from treating compliance as an audit exercise instead of an operational discipline embedded into engineering, security, and governance, including overlooking container runtime hardening that controls how containers execute, isolate processes, and apply security boundaries in production.
- Treating SOC 2 as documentation-only rather than implementing real, testable controls across infrastructure and workflows.
- Mis-scoping environments and assets, assuming one control set applies to every SOC 2 requirement regardless of architecture or service model.
- Building controls for the audit instead of production realities, which creates operational friction and weak adoption.
- Ignoring access design early, leading to over-privileged systems and delayed remediation during audit preparation.
- Implementing tools without defined control objectives, resulting in fragmented evidence and inconsistent processes.
- Failing to operationalize monitoring and incident workflows, which reduces trust in control effectiveness.
- Treating readiness as a one-time milestone instead of a continuous process aligned with product changes.
- Overlooking third-party dependencies and shared-responsibility risks in cloud-native environments.
- Delaying leadership ownership, which weakens governance and slows cross-team execution.
- Misunderstanding what SOC 2 offers—it is a trust and assurance model, not a certification badge or purely compliance-driven exercise.
FAQs
- What role do containers play in SOC 2 scope definition?
Containers define system boundaries, data flow paths, and runtime risks, which directly influence control mapping, monitoring scope, and audit evidence requirements.
- Does SOC 2 apply to internal SaaS tools or only customer-facing platforms?
SOC 2 can apply to internal platforms if they process production data, support customer environments, or influence service delivery reliability and security.
- How early should a SaaS startup begin SOC 2 preparation?
Preparation typically starts before enterprise sales or vendor due diligence, when security posture and governance begin influencing procurement decisions.
- Can SOC 2 coexist with other security frameworks in a container environment?
Yes. Organizations often align SOC 2 with broader security and compliance programs to support operational consistency and multi-framework readiness.
- How do multi-tenant SaaS architectures affect SOC 2 implementation?
They require stronger isolation, access design, monitoring, and tenant-level risk controls to prevent cross-environment exposure.
- What operational signals strengthen SOC 2 audit readiness for container platforms?
Consistent logging, access traceability, incident response maturity, configuration governance, and verifiable control execution strengthen audit outcomes.



