OCI Image: Definition, Format, OCI, Differences, Benefits, Works
This article breaks down the OCI image format and why the Open Container Initiative matters. It explains the OCI specs, how OCI compares to Docker images, what manifests and layers do, how registries distribute artifacts, and how to make OCI packaging predictable and verifiable.
What is OCI image format?
OCI image format stands for Open Container Initiative (OCI) standard image format specification that defines how a container image is packaged, described, and verified so different tools can build image artifacts with the same manifest, config, and layer digests, then move and run the same oci image consistently across environments (for example, a Linux server running containerd can pull and run the same image that a CI pipeline pushed to a registry).
What does OCI image format mean in container packaging?
OCI image format in container packaging means you package an application as a standard, tool-neutral artifact defined by the OCI image specification (the image-spec published on GitHub), so any compliant tool can store, move, and validate it the same way.
This is “packaging” because it standardizes what the image is and how it is described. The separate runtime specification (used by an oci runtime) defines how to run that packaged image as a container. In practice, docker and other tooling can exchange these images because they follow the same OCI spec-defined structure.
What is the Open Container Initiative (OCI)?
The Open Container Initiative (OCI) is an open standards body that publishes the OCI specification (specs) that make container artifacts portable across tooling by defining what an image is and how a runtime should execute it, which strengthens container security by making image contents and runtime behavior predictable, verifiable, and consistent across different tools and environments.
In practical terms, OCI standardizes:
- Image packaging: the image spec defines a JSON manifest and config that reference ordered filesystem layers by cryptographic digest, so the same image contents can be verified and reproduced when pulled or moved, which enables container scanning tools to scan a specific image digest and reliably match the findings to the exact layers and packages that will run in production.
- Runtime execution: the runtime specification defines the runtime configuration (commonly a config.json) that a compliant runtime uses to start a container consistently on a host OS.
OCI image vs Docker image: What’s the difference?
Here is the difference between OCI image and Docker image, and it also helps to clarify docker image vs container by showing that an image is the packaged, immutable filesystem plus metadata, while a container is the running instance created from that image at execution time.
What are the OCI image spec, runtime spec, and distribution spec?
The OCI project defines three complementary specs that cover what an image is, how it runs, and how it is moved between systems.
- OCI image spec (image-spec)
Defines the contents of a container image and how it is represented. It standardizes the image manifest (the manifest contains references to the image layer blobs and the image configuration), the optional image index for multi-platform images, and the image layout for storing images on disk. This is the spec a tool uses to build container images and describe them consistently, even when the image is used “like Docker”.
- OCI runtime spec (runtime-spec / OCI runtime specification)
Defines how to run a container from a prepared filesystem on a host. It standardizes the runtime bundle (a directory with a config.json plus a rootfs/), and the settings that a container runtime that implements the spec uses to start the process (for example on Linux, namespaces and cgroups are configured by the runtime based on config.json). This is what “running container” means at the execution layer for container runtimes.
- OCI distribution spec (distribution specification / oci distribution)
Defines the API protocol to facilitate and standardize the distribution of OCI artifacts between clients and a container registry. It standardizes push/pull flows for content-addressed blobs and manifests so a container engine or build system can upload and fetch images from registries (for example Docker Hub is a container registry implementing compatible distribution behavior).
What are the benefits, use cases, and limitations of OCI compliance?
OCI compliance means a container image and related tooling follow the shipping container image format spec defined by the OCI image format project under the Linux Foundation, so the image can be stored, moved, verified, and executed consistently across the container ecosystem.
Benefits
- Interoperability across tools and platforms: A compliant image can be built by one toolchain and run by another (for example, an image built in a CI pipeline can be pulled by Kubernetes nodes using containerd on Linux without format translation).
- Reproducible, verifiable image contents: The image manifest contains references to an immutable config and each blob in the set of filesystem layers by digest, so the contents of an image can be validated after pull, which makes containerization reliable by ensuring the same packaged application bytes are pulled and run across laptops, CI runners, and production nodes (for example, a registry returns the same manifest digest for the same release tag).
- Efficient distribution and caching: Because layers are content-addressed, shared base layers (for example, a common glibc layer across multiple services) are downloaded once and reused across images on the same node.
- Standardized distribution behavior: The oci distribution spec project defines the API contract for pushing and pulling manifests and blobs, which reduces vendor-specific behavior across registries.
Use cases

- Multi-architecture shipping: One image reference can support linux/amd64 and linux/arm64 via an index, letting the same deployment manifest run on mixed node pools.
- Cross-registry portability: The same image can be mirrored between registries (for example, from a public registry to a private production registry) while keeping digest integrity.
- Supply-chain auditability: Teams can pin deployments by digest rather than mutable tags, so production runs the exact bytes that were approved in release review, even when the Dockerfile used to build the image changes later, because the digest identifies the built image output rather than the build instructions.
Limitations
- Compliance does not guarantee security: OCI compliance proves packaging and reference integrity; it does not prove the image is vulnerability-free or that secrets are not embedded in layers.
- Runtime behavior still depends on the runtime and host: OCI images standardize packaging, but execution depends on how the runtime applies isolation and how the image is unpacked into a root filesystem; the OCI runtime bundle is where execution settings are enforced.
- Tag semantics remain mutable: Even with OCI compliance, a tag can be reassigned; digest pinning is required when you need immutable release guarantees across the container lifecycle, from build and registry promotion to deployment, rollback, and incident response.
What are the main components of an OCI image?
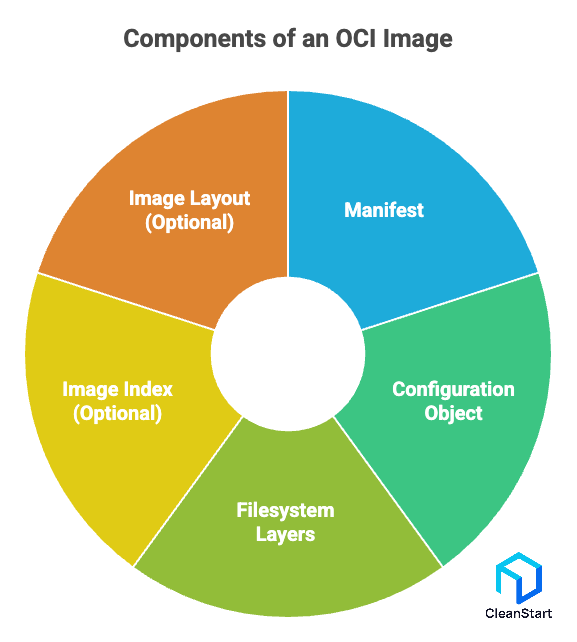
The main components of an OCI image are the standardized objects that define an OCI image for software shipping container image format portability across tools and operating systems, including configuration metadata such as the container entrypoint that specifies the default process the runtime should start when the image is executed.
- Manifest: a content-addressed document that lists the exact blobs that make up the image. In practice, a high-level OCI implementation would download an OCI image by fetching this manifest first, then using it to fetch the referenced blobs.
- Configuration object: metadata that describes how the image should behave when executed (for example, default process arguments and environment), which is needed before the image is unpacked into a runnable filesystem, and it also improves container monitoring because you can map the expected entrypoint process and runtime environment to what telemetry agents should observe at startup.
- Filesystem layers (blobs): ordered changesets that build the image’s filesystem; layers enable reuse and copy-on-write behavior when different container images share the same base content, which directly affects pull time and file size.
- Optional image index: a multi-platform entry that points to multiple manifests (for example, separate images for linux/amd64 and linux/arm64) under one reference.
- Optional image layout (on-disk format): a standardized directory structure for storing the image as blobs plus references, used to manage container images outside a registry or to move images between systems.
These are image components. Separately, when you run the image, the image is unpacked into an OCI runtime filesystem and becomes the container root, then a runtime bundle is created and run by an OCI runtime according to the runtime specification, and container networking is then configured by the runtime and orchestrator to attach the running container to the correct virtual network, DNS, and service endpoints.
How do you build, export, and convert OCI images?
You build, export, and convert OCI images by producing an OCI-structured image (manifest, config, layers), where container image layering breaks the filesystem into reusable, content-addressed layers that can be cached and shared across builds, optionally exporting it as an OCI image layout, and translating between OCI and Docker media types or transports when needed.
- Build an OCI image (OCI media types)
Build and push with OCI media types enabled: docker buildx build --output type=image,name=<registry>/<repo>:<tag>,push=true,oci-mediatypes=true .
Build with an OCI manifest/config format (Podman defaults to OCI): podman build --format oci -t <repo>:<tag> .
- Export an OCI image (OCI image layout)
Export as an OCI image layout tarball: docker buildx build --output type=oci,dest=./image.oci.tar .
If you need a local archive from an existing image: podman save --format oci-archive -o ./image.oci.tar <repo>:<tag>
- Convert OCI images (between registries, layouts, and Docker v2)
Copy and convert between remote registries and local OCI layouts without loading into a local daemon: skopeo copy docker://<registry>/<repo>:<tag> oci-archive:./image.oci.tar
Convert Docker-default media types to OCI media types at build time (when you want the output to be OCI-typed): oci-mediatypes=true on Buildx image or registry exporters
How does an OCI image manifest work?
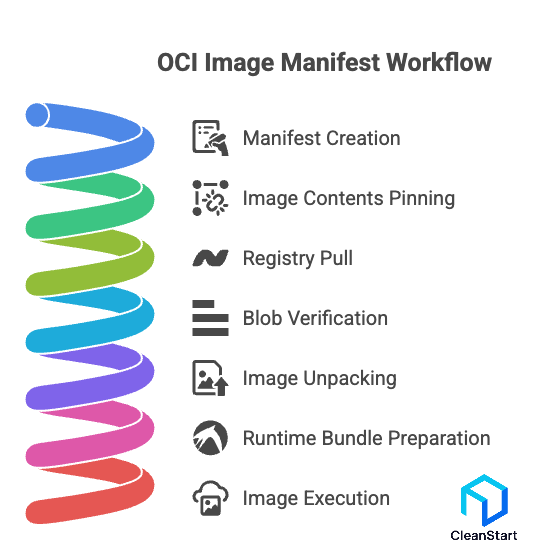
An OCI image manifest works as the content-addressed bill of materials for a container image. It is the object that lets tools implement the OCI standards around container formats in a reproducible way.
In practical terms, the manifest does three jobs:
- Pins the exact image contents: it lists the config object and each filesystem layer as immutable blobs referenced by cryptographic digest (commonly sha256), so “the same tag” resolves to the same bytes when you need container orchestration platforms like Kubernetes to roll out the same verified image across every node during production deployments.
- Enables registry pull and integrity verification: a high-level OCI implementation would download an OCI image by fetching the manifest from a registry first, then pulling the referenced blobs. Each blob is verified against its digest, which prevents silent corruption during transfer. This is the same workflow you use when using Docker to pull images, because modern tooling follows industry standards for content-addressed artifacts.
- Connects packaging to execution: after the layers are downloaded, the image is unpacked into an OCI runtime filesystem (the rootfs) starting from the base image layers that provide the initial OS userland files and libraries, then the runtime bundle is prepared (bundle directory plus config.json) and run by an OCI runtime; the runtime specification outlines how to run that bundle, not how the image is packaged.
What is OCI image configuration, and what does it contain?
OCI image configuration is the metadata object that describes how a container should behave when the image is executed, and it is referenced by digest from the image manifest so tooling can reproduce the same runtime defaults consistently.
It typically contains:
- Execution defaults: the default process to run (entrypoint and command), environment variables, working directory, user, exposed ports, and stop signal. For example, an NGINX image configuration commonly sets an entrypoint that starts nginx in the foreground, so a Kubernetes Pod starts the intended process without extra flags, as long as the image is pulled from the correct image repository that stores the intended tagged or digest-pinned release for that deployment.
- Root filesystem metadata: the ordered list of layer diff IDs that define the final filesystem state, which is used to validate that the unpacked rootfs matches the expected content.
- Build and history metadata: creation time and layer history entries that help explain how the image was assembled, which is useful when auditing changes across releases.
In the OCI flow, a high-level implementation would fetch the config object (by digest), then download the layers, then unpack the image into a runtime filesystem, and finally point the OCI runtime bundle at that rootfs before the runtime bundle would be run by an OCI runtime, while an SBOM generated for that exact image digest lists the included packages and versions so security teams can audit what is inside the pulled image before it is deployed.
What are OCI layers and filesystem layers?
OCI layers are content-addressed blobs that represent ordered filesystem changes used to build a container image in a reproducible way. Filesystem layers are the same concept viewed from the OS perspective: each layer is a tar archive of file additions, modifications, and deletions that, when applied in order, produces the final image filesystem.
Key points:
- What a layer contains: a filesystem layer typically includes paths like /usr/lib, /app, or /etc, plus metadata such as file permissions and ownership. For example, a build step that installs curl adds files under /usr/bin/curl and related libraries into a new layer.
- How layers are referenced: the image manifest references each layer by cryptographic digest (commonly sha256), which is why OCI layers support integrity checks and caching across pulls, and a hardened container image benefits directly because every secured layer you publish is pinned and verified by digest, preventing unnoticed drift when the image is pulled and deployed.
- How layers become a runnable filesystem: a high-level OCI implementation would download the layers, verify digests, then unpack them and stack them into a single root filesystem using a union filesystem (for example, OverlayFS on Linux). This layering model is a core part of industry standards around container packaging because it enables reuse and efficient distribution.
What is the relationship between OCI, the Linux Foundation, and the cloud native ecosystem?
OCI is a Linux Foundation hosted project that publishes vendor-neutral container standards, so organizations can adopt containers without locking into a single toolchain, including packaging distroless container images that remove shells and package managers to reduce the runtime attack surface while still remaining portable across OCI-compliant tools.
The cloud native ecosystem builds on OCI because OCI defines the common contract between build tools, registries, and runtimes, so a Linux Container can be built once, stored in a registry, and executed by different runtimes on Linux hosts without changing the image format.
- OCI sets the standards: OCI defines open standards for container formats and runtimes, which is why the same image and runtime model can be implemented across multiple vendors and projects.
- Linux Foundation connects the ecosystem: CNCF is “part of the Linux Foundation,” and it hosts many cloud native projects that depend on OCI-compatible runtimes and images (for example, Kubernetes + containerd + runc in production clusters).
- OCI is the interoperability layer: in a typical Kubernetes deployment, nodes run containerd (a CNCF project) which executes containers via OCI runc, using OCI specs as the runtime boundary between higher-level orchestration and low-level process execution.
FAQs
- Can OCI images be signed, and how are signatures tied to the exact image bytes?
Yes. Teams sign the image digest (for example @sha256:<digest>), so verification checks the exact manifest and layer set instead of trusting a mutable tag.
- Can an OCI registry store SBOMs or provenance attestations for an image?
Yes. Many teams store an SBOM or provenance as an OCI artifact linked to the image digest, then enforce policy in CI or admission (for example, block deploy if the digest lacks an approved attestation).
- What is the difference between an OCI image layout and an image stored in a registry?
OCI image layout is an on-disk package (for example index.json plus blobs/sha256/...) you can move offline; a registry stores the same blobs behind an API for push/pull workflows.
- How do you deploy an OCI image immutably in Kubernetes?
Use a digest reference (for example repo/app@sha256:<digest>), so every node pulls the same bytes across rollouts, rollbacks, and incident response.
- If OCI and Docker are often compatible, when do you still need image conversion?
When a tool or registry expects a specific manifest media type, or when you must export as an OCI layout for air-gapped transfer; conversion mainly changes the manifest framing, not the underlying filesystem layer bytes.
- Which OCI specification defines the format of a container image?
The OCI Image Specification (image-spec) defines the format of a container image, including the manifest, configuration, and filesystem layer structure.



